The FCC has banned all new consumer routers made outside the US, leaving networks stuck with aging, insecure hardware while blocking innovation. Find out why this sweeping move is raising eyebrows and lawsuits—and why it makes zero sense for cybersecurity.
- Apple's 26.4 age queries catches many by surprise.
- LinkedIn's 2.7 MB of privacy-invading javascript.
- Microsoft starts forcing Win11 24H2 to 25H2.
- Cisco loses source code to the Trivy supply-chain mess.
- Proton introduces privacy-first voice and video "Meet."
- GitHub to fix lagging security of its Actions feature.
- Cloudflare reaffirms the privacy of its 1.1.1.1 DNS.
- Cloudflare uses AI to re-code better secure Wordpress.
- The FCC drops a ban on all new consumer-grade routers.
Show Notes - https://www.grc.com/sn/SN-1073-Notes.pdf
Hosts: Steve Gibson and Leo Laporte
Download or subscribe to Security Now at https://twit.tv/shows/security-now.
You can submit a question to Security Now at the GRC Feedback Page.
For 16kbps versions, transcripts, and notes (including fixes), visit Steve's site: grc.com, also the home of the best disk maintenance and recovery utility ever written Spinrite 6.
Join Club TWiT for Ad-Free Podcasts!
Support what you love and get ad-free audio and video feeds, a members-only Discord, and exclusive content. Join today: https://twit.tv/clubtwit
Sponsors:
[00:00:00] It's time for Security Now. Steve Gibson is here, amazed at the large privacy-invading JavaScript blob LinkedIn is forcing on people. We'll talk about that. And what does Steve think of the FCC router ban? Hmm, that's coming up next on Security Now. Podcasts you love. From people you trust. This is TWIT.
[00:00:29] This is Security Now with Steve Gibson, Episode 1073, recorded Tuesday, April 7th, 2026. The FCC Bans New Consumer Routers. It's time for Security Now, the show where we cover the latest security, privacy and other stuff with this guy, right here, Mr. Steve Gibson. It is true, my friend. It is true. It is once again, once again, Tuesday.
[00:00:57] Uh, yeah. How did that happen? Yeah. Well, well, Leo, if 168 hours go by. And it hasn't always been. I like being here on Tuesday. It used to annoy me when we were on, I think we're on Monday for a while and three day weekends would kill, would cancel a podcast. No, this is a good day. Hey, you know what? If a Wednesday would work better, you just let me know. No, no. I'm here for you, Steve. We're good. We're good. I know that would upset everybody else's like,
[00:01:25] you know, it upset Paul when we moved from Tuesday to Wednesday. He said, what are you talking about? Just okay. So, um, the big topic for actually from a week before, uh, from our listeners, I just didn't have a chance to dig into it and get to it and look at it and talk about it was this bizarro
[00:01:46] sudden surprising FCC ban on new consumer routers. Uh, it's important that it's not existing consumer routers. No, it's like, anyway, we're going to talk about this. And, and by the time we're done with today's podcast, everybody listening will understand exactly what happened, why it doesn't really make
[00:02:11] any sense. Uh, lots of little, what I think about it's laced in there. Uh, several of our listeners did note that I did a poor job of wording the summary because in the little summary bullet points in the email that went out Sunday and is here at the top of the show notes, I said, the FCC drops a ban on all new consumer grade route. They adopted it rather than dropping it. I, yes, I understand.
[00:02:38] And I, you're, you're thinking is they dropped a ban on them, but of course that's got a, that's got a double meaning because they could, there could have been a ban, which they then dropped stopping the ban. I remember what the fortunately that I, I left hanging before the show began has to do with this. Fortunately, anybody who watches this show knows how to make their own router as you do. Yes. Yes. So we're not, I'm sure. Talk about that. Not concerned about that. Um, anyway,
[00:03:07] but we got a bunch of stuff to talk about as always, uh, we got the fact that Apple's 20, it's sort of notorious now 26.4. And, you know, if you just say 26.4 to an Apple person, they go, Oh yeah. Uh, it's caught many people by surprise. We've got LinkedIn's 20. Okay. 2.7
[00:03:31] megabyte privacy invading JavaScript blob, which is currently yes. Microsoft has just gone off the rails with this. We also have micro. I want a quick note about them forcing, uh, windows 11, 24 H two to 25 H two, uh, and the consequences of that Cisco losing their source code to, at the, or another casualty of this trivy supply chain mess that caught, uh, light LLM that we talked
[00:04:01] about last week. Uh, proton had a big fan, a big favorite of our, of our listeners, uh, has introduced a, what they're, what they're calling a privacy first voice and video service known as meet. Uh, uh, GitHub is going to respond to, to the other, this whole trivy Cisco light LLM mess by taking a closer look at the security of its actions feature, which is one of what's what was abused to make this
[00:04:30] happen and change their, their, their rollout schedule, uh, cloudflare reaffirming the privacy of its DNS service. Uh, and oh, Leo, they've recoded cloudflare. That is recoded WordPress. Oh, yes. Fix it. Yeah. Yes. M dash, which is a cute name for that. It is. It's a little confusing,
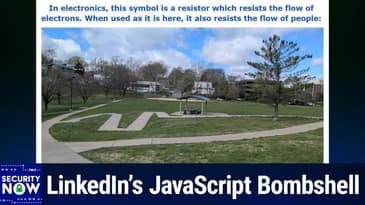
[00:04:54] but now if you weren't, if you weren't into, you know, like, uh, I guess manually. Yeah, exactly. Typography and dash and M dash and so forth. So lots of stuff to talk about. We got a great picture of the week, which, uh, has been explained by a couple of our listeners. This was actually submitted by a listener who was walking by, saw this and thought, okay, I got to take a picture of this for Steve because you know, this is, this is wacky. I can't wait to see it. Uh, and I love my
[00:05:23] caption if I do say so. So anyway, we will, we will talk about it. We will get there. It is coming up next as we continue with security. Now for this, uh, Wednesday, April 7th, we are going to, uh, get to that in just a bit, but first a word from our sponsor, as they say, this episode of security now brought to you by, Oh, I love this company meter, the company building better networks.
[00:05:49] I talked to these guys was two, it was two network engineers who started meter. And the reason they started is they were so unhappy with the state of networking gear, uh, networking configurations, networking software. They said, you were going to have to do this ourselves. And they did. And you're, this is why you want to know about it. If you're a network engineer, they feel your pain,
[00:06:13] you know, you know, legacy providers, inflexible pricing. Uh, of course, everybody in it suffers from resource constraints, stretching you thin and networking is as vital as it is to the business is not immune to that. You've got complex deployments across fragmented tools. Look, the network is mission critical to the business, but you're probably working with infrastructure
[00:06:38] that just wasn't built for today's demands. Everything's changed, right? But that's why businesses are switching to meter meter designed from the ground up for modern networks today. And for tomorrow meter delivers, and this is the key full stack networking infrastructure. They do it all wired, wireless, cellular built for performance and scalability. That's because meter
[00:07:07] designs the hardware. They write the firmware, they build the software, they manage the deployments, they provide the support after sales and service. They do it all. In fact, meter will even do ISP procurement for you. They will do security, routing, switching, wireless, firewall, cellular. Uh, they do power. That's important, right? Clean power, critical DNS security. They do VPNs. They do SD
[00:07:36] WAN multi-site workflows. In fact, that's one of their specialties. I was talking to them and say a common problem is a company will acquire another company and, uh, you know, they get this big warehouse 500 miles away and they have to join the network. The warehouse is 40,000 square feet. It's, it's, you know, impossible Faraday cage and they can solve that. They can fix it and make it all work.
[00:08:04] Meters, single integrated networking stack scales from major hospitals to branch offices to those giant warehouses, big campuses, even, even data centers. In fact, Reddit uses meter for their data centers. Ask the assistant director of technology for web school of Knoxville talking about large campuses. They actually have two facilities. He said, we had more than 20 games on campus, athletic events on
[00:08:32] campus between our two facilities, each game simultaneously being streamed via wired and wireless connections. And the event went off without a hitch. He said, we could never have done this before meter redesigned our network. With meter. You get a single partner. This is nice to one phone number to call for all your connectivity needs from first site survey to ongoing support without the complexity of managing multiple providers, multiple tools.
[00:09:02] Meters integrated networking stack is designed to take the burden off your it team and give you deep control and visibility. Reimagining what it means for businesses to get and stay online. I mean, it's clear. Everything has changed. The network is mission critical. Technology's moved very quickly in this area. You need hardware. You need software built for the demands of today and tomorrow. And that is meter.
[00:09:30] Thanks to meter for sponsoring security. Now we appreciate that. And we appreciate it. If you go to meter.com slash security now and book a demo, you can thank me later. That's M E T E R.com slash security. Now to book a demo. These guys have worked it out. Meter.com slash security. Now, now it's time for the picture of the week.
[00:09:54] Okay. So the caption, you have to have the caption first because, uh, because I love this caption. I wrote in electronics, this symbol is a resistor, which resists the flow of electrons. When used as it is here, it also resists the flow of people. So I'm thinking it's a line with like a, like a spiral squiggle, right? Is there, is that a resistor? I think that's a coil actually. That's a coil. What's the resistor? Oh, it's the zigzag.
[00:10:23] The zigzag. Right, right, right. Yep. Right. Yep. Well, uh, why is I guess the question? So the, and so this is not, uh, I know it's, so it's, it's, it's a, clearly it's a resistor, right? I mean, that's what it is. It is a, it is a walking path resistor. Um, this, uh, several, uh, people wrote saying, I think this is AI generated. This is nonsense.
[00:10:52] Well, of course in this world, unfortunately it could well be AI generated work. I'm afraid that's just going to be the standard response to anything that looks bizarre from now on. But this was actually, this is a photo taken by a listener who, as I said, was walking by, saw this and thought, Oh, Steve's going to have fun. So, uh, and, uh, this was a Seth Smith, our, our listener sent it to me.
[00:11:16] Anyway, the, the best explanation I've had is that a straight line may have been too steep for getting by like a wheelchair or some, some sort of grade. It looks like there is a grade. So this is a switchback.
[00:11:40] And so code might require, yes, that, that they switch back and forth in order not to encounter a grade, which is too steep in order to roll themselves. Uh, if, if they were in some fashion handicapped up to that little table. So that, you know, sounds right, but it's not very well done. It's ugly. It feels like there was some, there's something missing.
[00:12:05] Like there might've been a reason for this at one time that no longer, and it's not rounded. It'd be nice if it, if, if, if the corners, the points were rounded and it looks like it's kind of pinchy up, up there at the very far one on, on, on the far right is like, it just doesn't look great. But anyway, uh, it is indeed a path resistor. So weird. Yeah. Very weird. Okay.
[00:12:32] So, uh, last week's Apple upgrade to release 26.4, uh, has sent age confirming shock waves through the UK. And in fact, I even got one. I'm trying to think what it was I was doing. I was doing something. I low, I was logging into some app. Um, oh, I think I might've been installing Claude on, on an iPhone.
[00:12:59] And I got a short little pop-up that just notified me that, um, that the app had been informed that I was over 18. And I, Oh, interesting. Oh yeah. Yeah. And, and, you know, I had occasion as a consequence of all this to go into my settings and I, I, you know, I am there. It shows my name under my Apple account for Steve Gibson shows my name and my birth date is, you know, it's in the phone.
[00:13:29] So the phone knows how old I am. So anyway, so a listener of ours, Dan Bright in Scotland, he sent an email said, hi, Steve, just FYI. Although you likely already know I'm in the UK and updated my phone to 26.4 to be immediately presented.
[00:13:49] With an age verification process, which I'm instructed needs to be completed to enable age restricted content settings to be changed. Please find screenshot attached. And he sent me a screenshot and this is, you know, an iPhone, uh, and a good for you, uh, uh, Dan it's your, your phone is being kept charged. We know that large lithium ion batteries appreciate you keeping the phone charged.
[00:14:19] Um, uh, so it says confirm your 18 plus UK law requires, and I'll just note that it actually doesn't, but okay. UK law requires you to confirm you are an adult to change content restrictions by continuing your ID or credit card may be used to confirm you're an adult.
[00:14:39] And there's a, uh, you know, a big group, a big, a big blue click to continue, or you can defer that and confirm later and, or learn more about that. So, uh, also somebody using the handle red over in GRC's security now news group posted. I am in the UK have had an Apple account for more than 18 years as I had an original iPod touch.
[00:15:07] And he said, electronic, similar to original iPhone. And after installing iPad OS 26.4, the system said, quote, your Apple account is older than 18 years. You are good. That's great. And he said, he said, I wonder if that's a good method of doing age verification. Lots in the UK report problems. Lots of people don't have credit cards as you need to be 18 to have credit.
[00:15:37] So that's a common check. He said, and Apple system doesn't accept a UK passport as proof of age. And there was, I think that might've just changed app. Apple's been iterating on this because of the problems and the feedback that they've been receiving. Once this went out to a much wider, uh, audience, I poked around the internet, uh, reading feedback on the guardian nine to five Mac and elsewhere. Nothing stood out as worth sharing in greater detail.
[00:16:06] If I were to sum it all up with a generalization, um, I, I sort of call the nature of the reactions. Get off my lawn. Um, you know, normies who don't listen to this podcast and who have not had any reason to track the rapidly changing landscape of online age verification.
[00:16:25] Certainly as we have been, uh, they'll be understandably surprised and annoyed by this apparently sudden need for their eye devices to need proof of their ages. It's like, what, why, what, huh? So for those who've been paying attention, of course, or listening to this podcast, this won't be any surprise at all. One way or another, it will be coming to every device we own.
[00:16:52] As I noted last week, even reliably re-identifying an anonymous user remotely across a network known as authenticating has proven to be a challenge. Now we're needing to reliably and anonymously assert anyone's age, which is, you know, another like whole level. Uh, in my opinion, as I've said, what Apple, I believe what Apple has done is exactly the right thing.
[00:17:22] You know, it's true. This will annoy some people. Nine to five Mac quoted a reader of theirs who commented on their coverage. This guy wrote, this is quite a big failure by Apple. I use a debit card rather than a credit card. I've had one from the same bank for almost 40 years. I don't have a photo driving license.
[00:17:47] My Apple account is about 14.5 years old, meaning not 18 like Red's was who I shared before. He said, I can't verify my age despite being just over 60, six zero years old. Even if they had a passport, which should have been usable from the start. I don't have one of those either. As far as I understand, age verification is not required at device level, at least not yet.
[00:18:17] So Apple could either remove it or make it opt in. Whilst I can see how it's easier to have it on your device. So not having to verify age for all restricted websites and age related purchases. It needs to work for all or not be forced on us. Besides kids will find ways around it.
[00:18:40] And for now, from what I've seen, you could still get separate age verification for websites outside of Apple unless they try to block people doing that. Right. So as I said, get off my lawn. You know, he said it needs to work for all or not be forced on us. Right. A hundred percent. That would be great. But there's no magic solution. Right.
[00:19:06] Partly people are freaked out over any perceived loss of their largely fictitious anonymity online. Partly people are upset over the imposition of any restriction of any kind over what they could do online. They've never had any before. So now why all of a sudden? You know, are some freedoms being taken away from us and some restrictions imposed? Yeah, they are.
[00:19:34] But everyone should blame their democratically elected politicians. The old adage, you know, I'm not shooting the messenger applies here. The technologies are just doing the best they can to implement what the emerging regional laws require. As societies, we want to protect our children from all the nastiness the world harbors. The anonymity that the Internet offers to criminals means that the Internet is likely to always contain more than its fair share of bad actors.
[00:20:03] Just as it does today. That's unlikely to change. So. Might some of us like this guy who grumbled to nine to five Mac be inconvenienced by our collective desire to manage what kids can access online? Uh huh. Yes, that's going to happen. But that's the relatively small price we need to pay. I don't see any way around it. And I love the idea that Apple is finally stepping up to this challenge.
[00:20:30] Having our platforms able to make these assertions for us globally and anonymously is the way to go. All of this discussion of the age of our Apple accounts made me wonder whether there was any way for us to determine how long we've had our accounts. Since I have a credit card register with Apple, they know I'm over 18.
[00:20:54] But since there are others who might be using debit cards like this nine to five Mac guy and may not have photo IDs or not have one that Apple understands, because there were some reports of that in the UK also. It appears that it's possible to bring up a web page at privacy dot Apple dot com.
[00:21:17] You'll be asked to log in with your Apple credentials, then respond to a multi-factor prompt on one of your Apple devices. Once you've done that, you'll be taken to a choose the data you wish to download page. I have a picture of that at the bottom of page three in the show notes. And this is I've never seen this page before.
[00:21:41] It's an amazingly comprehensive information request portal where you're able to download all sorts of information and data that Apple may have gathered and accumulated about you through the years of your account ownership with them. The one item you reportedly because I haven't been I've I've started the process. I haven't it hasn't finished because it takes it can take up to a week.
[00:22:08] The one item you need to select is Apple account and device information. But boy, there's a lot more if you want more. So I selected that one and press continue at the bottom of that very long and comprehensive page of things that I could request to receive from Apple. In fact, the list was so long and comprehensive that I was next asked how large a file I would be comfortable downloading.
[00:22:34] It defaulted to one gigabyte, in which case it sends you however many one gigabyte files you need. But I chose the maximum offering of 25 gigs because the file isn't emailed. Once Apple has assembled the information, I then receive another email needing. Now I need to log in again to reprove my identity. Then I receive a link to download whatever Apple has to share with me.
[00:23:02] Since I initiated this just last Saturday afternoon, so three days ago, and it's expected to take as much as a week. I'm unsure, you know, when I'll have results to share probably by this time next week. And I'll just quickly let people know what I what I got. But anyway, I just wanted to share all that in case anyone listening might also be curious to know how long they've had their account. I wasn't quick to jump on an iPhone.
[00:23:32] I don't think I ever had an early iPod. You know, I was in love with my BlackBerry. I was one of those pry this from my cold, dead. Do you still have some in your freezer? No, I don't. And I actually did get there is a physical keyboard for the iPhone. Did you order that? Yeah, I tried it. It's it's crap. It's no good. Besides, it makes your phone about I can't show it. It's dorky.
[00:24:00] Yeah, it's like it's really like weird. It's like, you know, a foot long and sticks out of your pocket. So, no, it's it's not going to go. I cannot use the iPhone keyboard. I hate it. It is the it is the biggest trade off that. But, yeah, I mean, I get it that that's what they want to do. And remember, of course, it was meant to be a consumption device, theoretically. But now I know I do have a Bluetooth keyboard that is a full size keyboard.
[00:24:30] It's a cute little thing from Logitech. That guy. Oh, that's nice. Yeah, it is. And it allows you to associate itself with up to three different devices and you choose which one you want. So so so it can appear as one of three different keyboards. And so if I know I'm going to be typing something at length, normally, though, I'll just do I was like I'm so annoyed.
[00:24:53] Also, Leo, with this schism between iPhone and Windows, like Apple just refuses to accept the fact that Windows owns the desktop and they're only willing to connect to their Mac in a in a seamless fashion. So I'll like write something long, then I'll email it to myself, get the email on my phone, select it all, drop it into message and send it. It's like, God, really? This is what I'm being made.
[00:25:21] It's one of the reasons I'm so annoyed with Apple. But yeah. Apparently, you can also look at your purchases on the on the Apple ID and see when the oldest purchase you made. Yes. Apparently, everything I mean, this is all their age is so comprehensive. So I just thought it was cool. I didn't know. I'd never gone to privacy dot Apple dot com and done that. But if someone wants to know how long they've had their account, I'm.
[00:25:49] I don't remember when we began the podcast, that would be an interesting I know that we began a podcast in 2005, but I don't remember whether I had an iPhone. I don't remember when I was a smartphone by that time. Well, they didn't come out until 2006. So I know you didn't have an iPhone in 2005. Oh, OK. Yeah. So I was still BlackBerry, happily carried my BlackBerry around. The most you could have would be 20 years worth of iPhone. Because actually, next year is their 20th anniversary. Oh, OK. And I probably waited a couple of years.
[00:26:19] Because, again, I just like giving my little BlackBerry. Well, you didn't know that you had to prove you were 18 until now. Well, that's true. I want to this next piece, LinkedIn and what Microsoft has done is long. Let's take a second break.
[00:26:38] And then I'm going to plow into some research that a disgruntled add on developer posted. But despite of his disgruntlement, he's not wrong. And, Leo, what Microsoft is doing is, because they're the owner of LinkedIn, it's like, what?
[00:27:06] Well, we'll talk about it in just a bit. What? But first, a word from Zscaler, our sponsor for this segment of Security Now, the world's largest cloud security platform. We talk about AI all the time. The potential rewards of AI, especially for your business. I think it's safe to say these days, too great to ignore, right? But you don't want to ignore the risks either. The risk of losing sensitive data. Attacks against enterprise-managed AI.
[00:27:36] And there's also the issue of the generative AI, and we've seen this on this show already many times, increases opportunities for threat actors. They're using AI to rapidly create impeccable phishing emails, to write malicious code. Thank goodness sometimes it's buggy, but sometimes it's not. And to automate data extraction. I'll give you an example ripped from the headlines. In 2025, there were 1.3 million instances.
[00:28:05] 1.3 million instances of social security numbers leaked to AI applications. And I can tell you right now that you're at risk right now because tax time is a week away, and your employees are almost certainly uploading their tax returns, your tax returns, anybody they can find tax returns to AI saying, can you do my taxes for me? And what's on your tax return? Everything a bad guy needs to steal your identity.
[00:28:32] Last year, ChatGPT and Microsoft saw nearly 3.2 million data violations. And you can't really blame employees. We're not thinking, oh, it's dangerous to upload stuff to AI? That's dangerous? Yes, it is. It's time for a modern approach. Protect yourself with Zscaler's Zero Trust Plus AI. It removes your attack surface. It secures your data everywhere. It safeguards your use of public and private AI.
[00:29:02] And it protects you against ransomware and AI-powered phishing attacks. All of that. Check out what Siva, the Director of Security and Infrastructure at Zuora, says about using Zscaler Watch. AI provides tremendous opportunities, but it also brings tremendous security concerns when it comes to data privacy and data security. The benefit of Zscaler with ZIA rolled out for us right now is giving us the insights of how our employees are using various Gen AI tools.
[00:29:31] So, ability to monitor the activity, make sure that what we consider confidential and sensitive information, according to companies' data classification, does not get fed into the public LLM models, etc.
[00:30:11] Thank you, Shiva. That's Zscaler.com. Slash security. Steve? Okay.
[00:30:18] So, two weeks ago, while you were at RSA, Leo, Micah and I took a look at what we might term the super pixels being used by Meta and TikTok now, which cause their own JavaScript code to be quietly run in the browsers of anyone visiting any website that hosted those pixels. And I'm putting pixels in air quotes here because, well, I'm going to explain.
[00:30:47] I noted at the time, I noted at the time, two weeks ago, that the use of the term pixel was almost catching in my throat because what has evolved over time has rendered that term laughable. So, just so that we're all starting off on the same page here, the original idea was that a so-called tracking pixel could be hosted by a website that a user was visiting.
[00:31:13] That pixel was actually an HTML URL for a single true pixel-sized dot, you know, a one-by-one JPEG or JIF or PNG file. It might even be wider transparent since it didn't want to call any attention to itself. It just wanted to be on the page.
[00:31:36] Its entire purpose was to cause the user's browser to fetch that tiny little innocuous one-by-one image dot from some other third party's remote server. And so, just to be clear, it would be the visible website the user was visiting that would be delivering its pages to its visitors, which contained the reference to that off-site third-party pixel.
[00:32:05] And since that pixel was referencing an image resource from another hosting domain, the user's browser would quietly be making that request to retrieve that pixel on behalf of its user. Now, we might wonder why the site being visited by its users might wish to add someone else's invisible pixels to its own pages.
[00:32:31] And the somewhat distressing answer is that the site would be receiving payment by that third-party site in return for the addition of those simple tiny pixels. So, the obvious next question is, why would some third-party site be willing to pay first-party sites who people visit all across the Internet in return for hosting their little all-but-invisible pixels?
[00:33:00] And the answer to that, of course, is tracking. This was the emergence of the early Internet tracking economy. When the user's browser requested that tiny little invisible pixel from the remote third-party server, its request contained a bunch of metadata information. The request's referrer header would identify the entire URL of the page the site's visitor was viewing.
[00:33:29] And the request's cookie header would dutifully return the unique third-party cookie that the third-party site may have previously given the user's browser to hold, assuming they had countered a little one of these little pixels from that same third-party site anywhere in the past. And, of course, the request would come from the user's IP address.
[00:33:54] So, lots of information available to some random, unaffiliated, not obviously affiliated third-party site. And all these little tracking beacons scattered far and wide across the Internet would be gathered by this third-party site, which could just sit back and aggregate all that data that was available to it.
[00:34:20] The final bit of horror, which we've covered here at the time, was that these tracking companies would create their own rewards and prizes and, like, sweep kind of, you know, sketchy sweepstakes websites where they would advertise across the Internet in order to draw people in.
[00:34:38] When signing up for their chance to win, you know, non-existent or maybe, you know, prizes, unwitting users would provide a ton of personal information to that site. You know, at least their names and email addresses and probably more. Sometimes their phone numbers, you know, because, hey, there's a chance to win.
[00:35:01] And since these bogus reward sites were being hosted by the same companies who were littering the Internet with their tracking pixels, all of that anonymous tracking data that had been aggregated over time, every website visited, the IP address that it had been visited from, the user's IP address, would then be all de-anonymized when the user provided their name and email addresses in return for essentially nothing.
[00:35:30] Unfortunately, those early days now look quaint. In retrospect, as users became aware that the sites they were visiting were secretly betraying them behind their backs, compromising their privacy by embedding a pixel in return for payment, browser extensions such as our favorite one, uBlock Origin, but also Privacy Badger, Ghostery, AdGuard, Disconnect, and NoScript
[00:35:57] were created to give users who cared some control over this egregious behavior. The next thing to happen was the evolution of the embedded tracking object from a relatively benign now, in retrospect, just a little JPEG, GIF, or PNG image pixel into a reference to a remote host's HTML or JavaScript.
[00:36:26] Arranging to run a third party's remotely supplied JavaScript now is the ultimate goal. And that can be done simply by directly referencing a third party JavaScript resource in the hosting page's HTML, HTML, you know, just whatever it is, .js for JavaScript. Just like a site's own provided JavaScript,
[00:36:50] the third party JavaScript will be loaded into and run by every page the user displays. The problem we have now is that we've invited foreign code to run inside our web browser, and the behavior of that code, the very code itself is subject to unilateral change by that third party at any time.
[00:37:16] And it is from such changes that the practice of web browser fingerprinting has evolved, right? It should now be clear why the continued use of the term pixel, you know, for anything meta or TikTok are doing is laughable. It's not a pixel any longer, although it still goes by that name. Now, what we have now is essentially hostile, uncontrolled,
[00:37:43] explicitly privacy compromising code execution by unseen third parties. That's the threat environment that users and their browsers face today. It's completely changed over the course of the last two decades. The duration of this podcast. We've seen all of this. One of the points I wanted to make before we turn to last week's news about LinkedIn
[00:38:08] is just how much this behavior is completely hidden from anyone who's clicking links and wandering around the web. You know, the expression out of sight, out of mind has never applied more than it does here. This unseen behavior has been a problem since the first use of a third party cookie for surreptitiously tracking user movement across the web. Through the intervening decades, such behavior has exploded.
[00:38:37] And the only thing that has any chance of reining it in on a wholesale level, not just like we who care running add-ons like you block origin, but like actually affecting everyone is government legislation, which will eventually wrestle this stuff to the ground, criminalizing it and just making it impossible to continue.
[00:39:05] And there we probably have the EU to thank because they tend to be pioneering this. They use pixel. Now, pixel is used kind of generically in the ad industry to anything that's tracking. We're often asked to put pixels in our podcasts, which obviously you can't do. You can't put pixels in an audio file. But there have been some audio beacons, though, haven't there? Well, and we do actually. In the feed, there are redirects.
[00:39:33] And that's as close as you can get. Yeah, it bounces you through something and then eventually. Exactly. Well, and in fact, PodTrack, you were using PodTrack in order to count downloads. That's exactly how we were counting downloads. Exactly. And we still do something similar. We don't do it with PodTrack. But yeah, that's exactly. So they call those pixels too. I always puzzle me when advertisers say, can you put a pixel in the podcast? And it's like, I don't think so. Yeah, because they're not, you know. Yeah. It's not a pixel.
[00:40:03] But they just mean tracking. And it's interesting too, because it does demonstrate how much they've just come to take it for granted. It's like, oh yeah. We want analytics. We want to gather as much data. Yes. Yeah. Well, talk about knowing everything, Leo. Wait till you hear this. Okay. Okay. So the examination of things that are going on behind people's back without their knowledge
[00:40:28] brings us to last week's LinkedIn revelation, which has been dubbed BrowserGate. Okay. Now this is by the apparently disgruntled developer who has a beef with LinkedIn's owner, Microsoft. The BrowserGate website is clearly passion driven. And its thesis raised some questions in my mind about its creator's motivations. Okay. But I'm getting ahead of the story. Let's first look at that website.
[00:40:56] It is at BrowserGate.eu. B-R-O-W-S-E-R-G-A-T-E dot E-U. So going there, we're first confronted with the bold black headline, LinkedIn is illegally searching your computer. Okay. The site then elaborates writing, Microsoft is running one of the largest corporate espionage
[00:41:26] operations in modern history. And now that may seem like it's a little over the top, but I don't think anyone's going to think that once we're through looking at this closely. He wrote every time any of LinkedIn's 1 billion users visits LinkedIn.com, hidden code. Okay. It's not really hidden. I mean, all code is hidden, right? We don't look at the code.
[00:41:51] No one does, but you know, so it's, yes, it's de facto hidden, hidden code searches their computer for installed software. That's true. That's true. Collects the results. That's true. And transmits them to LinkedIn server and to third party companies, including an American Israeli cybersecurity firm.
[00:42:16] The user is never asked, never told LinkedIn's privacy policy doesn't mention it because LinkedIn knows each user's real name, employer, and job title. It is not searching anonymous visitors. It is searching the computers identified people and identified companies, millions of companies every day, all over the world.
[00:42:45] This he's writes, this is illegal and potentially a criminal offense in every jurisdiction we've examined. Okay. So I want to, I want to share what this author claims is the behavior of LinkedIn's downloaded code. And for the record, none of this behavior appears to be in dispute. All of the evidence that they have collected is available for download and analysis.
[00:43:12] And it has been subsequently verified by independent researchers, including by bleeping computer who has the advantage of objectivity and knowing their way around. So under the heading of what we found, this author writes, mass breach of personal data.
[00:43:34] LinkedIn's scan reveals the religious beliefs, political opinions, disabilities, and job search activity of identified individuals. LinkedIn scans for extensions that identify practicing Muslims, extensions that reveal political orientation,
[00:43:56] extensions built for neurodivergent users, and 509 job search tools that expose who is secretly looking for work on the very platform where their current employer can see their profile. Under EU law, this category of data is not regulated. It is prohibited. LinkedIn has no consent, no disclosure, and no legal basis.
[00:44:25] Its privacy policy mentions none of this. LinkedIn scans for over 200 products that directly compete with its own sales tools, including Apollo, Luscia, and Zoom Info. Because LinkedIn knows each user's employer, it can map which companies use which competitor's products.
[00:44:50] It is extracting the customer lists of thousands of software companies from their users' browsers without anyone's knowledge. Then it uses what it finds. LinkedIn has already sent enforcement threats to users of third-party tools. Using data obtained through its covert scanning to identify its targets.
[00:45:13] In 2023, the EU designated LinkedIn a regulated gatekeeper under the Digital Markets Act and ordered it to open its platform to third-party tools. LinkedIn's response? It published two restricted APIs and presented them to the European Commission as compliance.
[00:45:37] Together, these APIs handle approximately 0.07 calls per second. Meanwhile, LinkedIn already operates a private internal API called Voyager that powers every LinkedIn web and mobile product at 163,000 calls per second. In Microsoft's 249-page compliance report to the EU, the word API appears 533 times.
[00:46:07] Voyager appears zero times. Meaning, he's saying that they're not acknowledging the use of this other internal API. At the same time, he writes, LinkedIn expanded its surveillance of the exact tools the regulation was designed to protect. The scan list grew from roughly 461 products in 2024 to over 6,000 by February of 2026.
[00:46:36] The EU told LinkedIn to let third-party tools in. LinkedIn built a surveillance system to find and punish every user of these tools. LinkedIn ships your data to third parties. It loads an invisible tracking element from human security, formerly Premier X, an American-Israeli cybersecurity firm, zero pixels wide, hidden off-screen that sets cookies on your browser without your knowledge.
[00:47:06] A separate fingerprinting script runs from LinkedIn's own servers. A third script from Google executes silently on every page download. Well, many people have that. But he says, all of it encrypted, none of it disclosed. And he finishes, Microsoft has 33,000 employees and a $15 billion legal budget. We have the evidence. What we need is people and funding to hold them accountable. Okay, so is this probably happening?
[00:47:35] As we'll see in a moment, apparently so. And thanks to the GDPR, much of what's being done behind the backs and without the explicit knowledge and permission of European Union citizens might well be illegal, as the creator of this website clearly believes. But knowing Microsoft, I would expect it to be covered by some vague consent to business purposes
[00:48:00] language, which anyone can take to mean anything, as we've seen. The good news is European regulators are genuinely and generally unimpressed by such implied consent. Okay, so to help us through this, you know, through a far less biased lens than this guy has, two days ago on Sunday, the Next Web did some great reporting on this.
[00:48:28] Even lacking the original author's bias, the Next Web's headline was, LinkedIn is secretly scanning your browser for 6,000 extensions and you weren't told. And just to give everyone a, so that we understand what we're talking about, it is actually reading, searching for files on a user's hard drive.
[00:48:54] It is looking through your file system when you go to a LinkedIn page, which is what Gleeping Computer confirmed and showed, you know, happening in their report of this. Is it part of its fingerprinting, you think? Or do they want that information? There's actually different fingerprinting than this. They apparently actually want to know what browser, Chromium browser extensions you have installed.
[00:49:22] So here's what, and the Next Web makes this clear. They said, every time you visit a Chromium-based browser, and actually Firefox users apparently are subjected to far less of this because it is very browser specific. Yeah, which is nice. Every time you visit LinkedIn in a Chromium-based browser, a hidden, again, they use the word hidden, but okay, JavaScript routine silently probes your browser.
[00:49:51] For more than 6,000 installed extensions. Collects 48 hardware and software characteristics about your device. That's the fingerprinting part. Encrypts the resulting fingerprint and attaches it to every API request you make during your session. The practice labeled browser gate by researchers is not disclosed in LinkedIn's privacy policy,
[00:50:17] says the Next Web, you know, who doesn't have a cross to bear here or axe to grind. LinkedIn says it's a security measure. Critics say it is covert surveillance of a billion users browsing behavior at industrial scale. There's a routine that runs on your computer every time you open LinkedIn. You cannot see it. You are not told about it.
[00:50:44] And it is not described in the company's privacy policy. According to an investigation published in early April, 2026 by far linked EV, a European association of commercial LinkedIn users. The platform get this Leo injects a 2.7 megabyte JavaScript bundle is like, it's like, wow.
[00:51:08] 2.7 megabytes of JavaScript into its website that silently scans visitors' browsers for the presence, and actually it's the visitors' PCs, for the presence of more than 6,000 specific Chrome extensions. Assembles a detailed fingerprint of their hardware, encrypts it, and transmits the result to
[00:51:33] LinkedIn servers where it's attached to every subsequent action taken during the session. The investigation, the Next Web writes, independently confirmed by bleeping computer, which verified the scanning behavior through its own testing, has been dubbed browser gate. LinkedIn disputes many of the report's characterizations. The technical facts, however, are not in dispute.
[00:52:00] LinkedIn calls its scanning system spectroscopy. When a user loads the LinkedIn website, the script fires off up to 6,222 simultaneous requests, each one probing for a specific browser extension by attempting to access files on the user's file system
[00:52:28] associated with that extension's ID. The presence or absence of a file in the response indicates whether the extension is installed. The entire operation runs silently in the background without a visible prompt or notification of any kind. Beyond, again, 6,222 extensions that it's checking for. Why?
[00:52:58] What business is it of LinkedIn? What extensions to that degree, more than 6,000 of them, that a user has installed? Beyond extensions, the script collects 48 distinct characteristics of the user's device. CPU core count, available memory, screen resolution, time zone, language settings, battery status, audio hardware information, and storage capacity, among others.
[00:53:28] Now, those are traditional, those are like standard fingerprinting, right? They said, individually, these attributes are unremarkable. Combined, they form a device fingerprint, true, specific enough to identify a user even after cookies are cleared. Okay? We've all seen that before. However, they said, once compiled, the data is serialized to JSON and encrypted using an RSA public key.
[00:53:57] LinkedIn's internal identifier for the key is APFC-DFPK. Before being transmitted to telemetry endpoints, including LI slash track and slash platform telemetry slash LI slash APFC-DF.
[00:54:17] The fingerprint is then permanently injected as an HTTP header into every API request made during the session, meaning LinkedIn receives it with every search, every profile view, every message sent. Okay, now I'm going to pause here a minute. They haven't looked at the code. I'm sorry, I haven't looked at the code. But what the next web described makes sense in an interesting way.
[00:54:47] They wrote that the data was compiled, serialized to JSON, and encrypted using an RSA public key. But my spidey sense tripped when I didn't see any mention of hashing. And I did see that mention of reversible encryption thanks to the use of an RSA public key.
[00:55:09] As we all know, the widely accepted way of fingerprinting a browser is to collect all of that random yet very specific data, then hash it down into an information lossy, thus irreversible hash. This creates a token that can be used to represent the user's browser as it moves about the web.
[00:55:37] But my first question is why Microsoft would need to have that at all. This sort of fingerprinting is only used by third parties who wish to track browsers as they move to other sites containing the same third-party fingerprinting code. But Microsoft's LinkedIn users are already logged in with a first-party relationship to Microsoft.
[00:56:05] So why would Microsoft need to track them anywhere? Doesn't make any sense there. It seems to me that this is not a fingerprint at all in the traditional sense. I think that it must be a form of what I will call a super fingerprint. Microsoft is assembling those 48 data points into a JSON object, which is then serialized.
[00:56:34] A random symmetric key will be derived and used to reversibly encrypt that serialized JSON blob. That symmetric key will then be encrypted with the RSA public key contained within that massive 2.7 megabytes of JavaScript.
[00:57:01] That means that at any later date, Microsoft or anyone else who might have the matching RSA private key, and they alone, can decrypt the original symmetric key, then use that to decrypt and deserialize the JSON object to obtain the original 48 individual pieces of information.
[00:57:30] Why would that be useful? Well, the problem with using a hash to fingerprint is that thanks to the magic of cryptographic hashing, deliberately so, if even one single bit of the hash's input data were to be changed, on average, half of the resulting hash's bits will be inverted.
[00:57:56] The point is that if just a single characteristic bit changes, an entirely new and untrackable hash results. But Microsoft's super fingerprint avoids the information lossy hash. So they've presumably retained all of the information contained within those 48 pieces of information individually.
[00:58:24] That means that Microsoft's super fingerprint can retain tracking or more likely a tight association with the user's browser, even when some of the browser's data changes. They change screen resolution. Their battery status changes, right? Because that's one of the things.
[00:58:47] The battery percentage change would completely result in a different hash in the old school fingerprint mode. Here, Microsoft can examine it, see that the battery charge changed, but nothing else did, and go, okay, same person. And then update the fingerprint to match the new battery status and continue tracking. So it is literally a super fingerprint.
[00:59:15] And since all this is sent back to the Microsoft LinkedIn mothership, what Microsoft probably does is fully decrypt all of that browser parameter data and keep it on file for every LinkedIn user. Over time, this would allow Microsoft to identify exactly how many and which web browsers each of their 1 billion LinkedIn users were to log into,
[00:59:43] since they're logging into LinkedIn. And perhaps that information could be useful for some security purpose. So that I can believe. The other thing that would also be interesting to check would be what exactly those 48 pieces of information are. I didn't dig into it. You know, that there could be a wolf hiding among the sheep. If the presumption was that everything was being hashed into a fingerprint,
[01:00:11] that none of the specific information that Microsoft was collecting could be a big deal, since that information would be lost due to the hash. Okay, you know, but if we assume that Microsoft is collecting and reversibly encrypting and forwarding all of that to their mothership, it would be interesting to see exactly what they're collecting and retaining. Because 48 individual things, that's a lot of things.
[01:00:40] You know, more than just screen resolution and battery charge and, you know, that kind of stuff. You know, browser user agent string and so forth. Anyway, the next web does have a bit more to say. They wrote, According to the browser gate report,
[01:01:10] LinkedIn's list includes more than 200 products that compete directly with its own, with LinkedIn's own sales tools. As noted before, Apollo, Luscia and Zoom Info. Because LinkedIn knows the employer of each registered user systematically scanning for the presence of a competitor's tools,
[01:01:34] gives the platform visibility, LinkedIn, visibility into which companies are evaluating or deploying rival products. Because again, they know who the LinkedIn person's employer is. The list also reportedly includes tools associated with neurodivergent conditions, religious practices, political interests, and job hunting activity,
[01:02:00] categories that in the European Union qualify as sensitive personal data subject to heightened protection under the general data protection regulation, you know, GDPR. Knowing that a user is running a job search extension, for instance, is a meaningful inference about their employment intentions drawn without their consent. The scale of the operation has grown substantially over time.
[01:02:28] In fact, this is really what's breathtaking. LinkedIn, they said, began scanning for 38 specific extensions in 2017. 38 extensions being scanned for in 2017. By 2024, that number had grown to 461. Hey, if some is good, more is better. Nobody seems to be minding or complaining, so let's just scan their hard disk more widely.
[01:02:57] By February of 2026, meaning a month and a half ago, the list had reached 6,167. Yes, 6,167 individual extensions files being scanned for. They wrote, bleeping computers testing confirmed the scanning was active as of early April 2026.
[01:03:26] I don't understand why they are looking for specific extensions instead of just saying, what extensions are you running? Can't you ask the browser what extensions are running as part of the fingerprinting? I think you can. It's weird. They're probably going beyond extensions. I mean, what they're doing… They're looking for all applications. They're looking for file names. They are doing file name queries. Oh, that's so weird. It is.
[01:03:55] And, Leo, I don't think I have a link here to the bleeping computer report, but you might grab it while I'm sharing this. Because it's bracing to actually see what… And I think it may have been Lawrence himself who did the research.
[01:04:14] So, now we're at, as of February 2026, we're at 6,167, which they note is a 1,252% increase in two years. Bleeping computers testing confirmed the scanning was active, as I noted, as of early April 2026. So, is this… Yep. That is…
[01:04:39] And you can see the IDs and then the files that are actually being scanned for. JavaScript, AVGs, HTMLs. So, those are actual file names. I kind of blame the browser for letting it do this. I agree. And that's where you're going to see me reach that conclusion here in a minute. That users need control over this completely out-of-control behavior. Yeah. Huh.
[01:05:08] So, they wrote… The next web wrote, LinkedIn's response to bleeping computer was pointed. A spokesperson said, quote, The claims made on the website linked here are plain wrong. The person behind them is subject to an account restriction for scraping and other violations of LinkedIn's terms of service.
[01:05:32] To protect the privacy of our members, their data, and to ensure site stability, we do look for extensions that scrape data without members' consent or otherwise violate LinkedIn's terms of service. So, they're saying they're looking at more than 6,000 extensions because they're naughty.
[01:05:57] And, okay, they said that they do not use the data to infer sensitive information about members. LinkedIn's… The next web wrote, LinkedIn's characterization of the source matters. Fairlinked EV is connected to TeamFluence, Signal Systems OU, an Estonian company whose managing directors are Stephen Morel and Jan Lebling.
[01:06:24] TeamFluence makes a Chrome extension, also called TeamFluence, that LinkedIn restricted for alleged terms of service violations. The company subsequently filed a preliminary injunction against LinkedIn Ireland Unlimited Company and LinkedIn Germany at the regional court of Munich, alleging violations of the Digital Markets Act, EU competition law, and German data protection rules.
[01:06:53] In January, the Munich court denied the injunction, finding that LinkedIn's actions did not constitute unlawful obstruction or discrimination. The financial dispute between the parties does not change the technical findings, however, which were verified independently. It does mean the framing of those findings is contested. The reader should weigh both the substance and the claim and its provenance.
[01:07:19] This is not LinkedIn's first serious encounter with European data protection enforcement. In October 2024, the Irish Data Protection Commission, which regulates LinkedIn in the EU through its Irish subsidiary, fined the company €310 million, approximately $334 million at the moment, for processing users' personal data for targeted advertising without a valid legal basis.
[01:07:48] So LinkedIn was found to be using personal data for targeted advertising. The decision found that LinkedIn's consent mechanisms did not meet GDPR's requirement that consent be freely given. LinkedIn was ordered to bring its data processing into compliance. The BrowserGate investigation drops into that context.
[01:08:11] The legal question of whether scanning for 6,000 browser extensions constitutes processing of special category personal data and whether users' lack of awareness of the practice renders any implied consent invalid is exactly the kind of a question the Irish Data Protection Commission has already shown it's willing to adjoin in court.
[01:08:38] Europe's evolving digital regulation framework has been moving steadily toward requiring explicit disclosure of all significant data collection and a scanning operation of this scale conducted without any mention in a privacy policy appears difficult to square with that direction of travel. LinkedIn is a Microsoft subsidiary, acquired in 2016 for $26.2 billion.
[01:09:06] Microsoft has been aggressively expanding its AI capabilities in 2026, with LinkedIn's vast data set of professional identity and employment history forming a significant part of the data infrastructure on which those capabilities rest. The relationship between LinkedIn's data collection practices and Microsoft's broader AI ambitions is not addressed in LinkedIn's privacy policy either.
[01:09:33] Anyway, so they talk about LinkedIn having more than 1 billion registered users. Oh, and they did note, short of using a non-Chromium browser such as Firefox, which would limit but not necessarily eliminate LinkedIn's fingerprinting capabilities, there is no user-facing setting that prevents the scanning.
[01:09:58] The platform does not offer an opt-out because it does not disclose the practice in the first place. The 2026 push for governed and transparent AI and data practices is built on precisely the premise that invisible data collection of this kind should not be the default.
[01:10:19] Okay, so we began this topic by, you know, reminiscing over the quaint web browser pixel, which was literally a pixel image dot supplied by some other domain's web server.
[01:10:37] That has evolved or perhaps devolved into an astonishingly monstrous and invasive 2.7 megabyte unsolicited blob of code that does actually, as observed, confirmed and reported by Bleeping Computer, scan the mass storage file system of its website's visitors.
[01:11:04] You go to LinkedIn.com, that happens to you, looking for the files, belonging to, at last count, and this is rapidly increasing, 6,236 web browser extensions, which are arguably none of its business. As the NextWeb stated, this may be illegal in the EU, where thankfully privacy regulations are very strong
[01:11:31] and are only getting stronger. But whether or not this is illegal, it seems pretty clear that things, and I agree with you, Leo, on this point, have gotten way out of hand, apparently due to a complete lack of adult supervision. Something really bizarre is going on at Microsoft's LinkedIn property. So regardless of the motivations of these begrudging developers,
[01:11:58] I'm very glad that the world has just received an absurdly clear example of the need to perhaps give our web browsers some form of control over what the JavaScript that the browsers are hosting is allowed to do. It would be nice if some sort of an alert came up and said,
[01:12:23] whoa, do you realize that the website that you have just gone to has made 6,232 queries of your file system? Like for different files by name of your file system? And how do you feel about that? Anyway, this JavaScript is rummaging around inside users' computers for a while,
[01:12:53] searching for all those files. Maybe we should be asked if we consent to having it do that. That just seems like crazy behavior on Microsoft's part, and they are only getting away with it because these people use the word hidden or secret. You know, it just isn't obvious. In the same way, the third-party cookies have never been obvious. So, you know, out of mind or out of sight, out of mind.
[01:13:20] And this has been certainly, you know, something no one would be aware of otherwise. It's crazy. But Leo? Yes. I know you know what our listeners do want to know about. They want more ads, right? Hey, I did want to mention this broke during the show.
[01:13:43] Anthropic, we know, was working on a new model of the rumors, mythos, and that the rumors were it was going to be so good that they were holding it back for fear it would be misused. Today, they announced that they are going to allow a small number of people to use mythos for security reasons.
[01:14:08] They say it is so good, strikingly capable of computer security tasks. They've already set it against existing browsers and operating systems, and they say found tens of thousands of vulnerabilities, including in operating systems that are in every operating system and every browser that is currently in use. So, of course, it could also be misused.
[01:14:38] Their fear is to find vulnerabilities that can be exploited. So they have announced something today called Project Glasswing, which they are going to, you know, let me go full screen on this. They're going to offer to a small number of companies. It is not going to be in wide availability, but they're going to offer to the good guys. The world's most critical software to find those vulnerabilities before the bad guys get access to this model.
[01:15:07] Now, Leo, we are living in a science fiction world. Well, this could be just really good marketing. I mean, understand what better way to say, hey, our model is good. But I think it's credible. And they say they've already found thousands of high severity vulnerabilities. They found Linux vulnerabilities have been around for 25 years. They found a free BSD escalation exploit that was very severe.
[01:15:35] So they are giving this away to a broad number of companies who have, you know, mission critical software in the enterprise. They're hoping that they'll find those vulnerabilities before it becomes, they become public. So it's going to be turned over to, you know.
[01:15:53] And I think what I read about this rumor at the time, because it wasn't officially disclosed, is this would be a super high end model that would cost more to use. Yeah. The rumor is it will be very expensive. We don't know. That's not been confirmed yet. They are dedicating $100 million in token credits to these companies so they can use it, you know, kind of freely. I think this is a big security story.
[01:16:22] Again, it could be just a very good marketing ploy. But I tend to credit that this is possible and that the scores on the software benchmarks for this thing are off the charts. Much better than their current 4.6 Opus. No kidding. Yeah. Even more so than Opus. Yeah, much more so. Like 50% better than Opus. Wow. So they found a 27-year-old OpenBSD bug. They found a 16-year-old FFmpeg bug.
[01:16:52] You know, I mean, we're going to see more and more of this, obviously. And the fear is that people will use it for, you know, to find those flaws and exploit them. So they want to give this away to people so that they can find them and fix them before they get exploited. So that remote code execution and the free BSD that's 17 years old. I mean. Remote code execution. Yeah. I thought it was a privilege. That's a different one. That's an OpenBSD. This isn't free BSD.
[01:17:19] This allows anyone to gain root in a machine running NFS from anywhere on the internet. So it's a pretty, and it's been around for 17 years. Wow. So they say fully autonomously, no human was involved either in discovery or exploitation of this vulnerability after the initial request to find the bug. So that's the concern. A bad guy will find it. And suddenly you've got all of these free BSD distros completely vulnerable.
[01:17:49] Yikes. 4.6 was able to exploit the vulnerability but required human guidance. Mythos did not. It could be. And that's really scary. The idea that they could autonomously. Well, I mean, there's no question that the bad guys will pay whatever the cost is and find exploits and jump on them. You know, we talked about exactly this.
[01:18:16] For a while, remember that I don't remember if it was OpenAI or Anthropic were saying that the good news is the AI seems better at finding problems than it is at exploiting them. That's not true anymore. That's not true anymore.
[01:18:59] That's apparently chained. That's true.
[01:19:27] That's true. There will be people who didn't check their code or that didn't qualify for Anthropic's initial offer. And bad guys, there's just no question that we're going to see a, you know, on the margins, there will be new exploits that are found.
[01:19:49] And I think, again, it could just be a marketing ploy, but I think I want to give credit to Anthropic for doing the right thing to hold this back and release it this way so that people had a chance. Otherwise, I'm afraid we don't have much of a chance in this modern world. Our show today brought to you by Material. I mean, talking about security, they are the cloud workspace security platform built for lean security teams.
[01:20:18] They're not there to replace you. They're there to support you. Managing security is hard enough, but doing it in the cloud is even harder. And phishing is not the only problem. Today's email security does the best it can, but it stops at the perimeter. And because when you're in a cloud environment, your email, your data, and your identity security tools are all siloed. So it's very hard to detect these attacks.
[01:20:43] Material crosses the barrier, protects email files and accounts in both Google Workspace and Microsoft 365. And that's because effective email security today needs to do more than just block phishing and other inbound attacks. It needs to provide visibility and defense across the entire workspace threat surface. So Material goes the extra mile.
[01:21:08] They ingest your settings, your contents, and your logs to give you holistic visibility into threats and risk across the workspace and the tools to automatically remediate them. Material delivers comprehensive workspace security by correlating signals and driving automated remediations across the environment. Yes, phishing protection, of course, and email security. Combining advanced AI detections with threat research, so you know ahead of time what's coming.
[01:21:35] And user report automation, so your users can be part of this. Detection and protection of sensitive data across inboxes and, very important, shared files. That's another threat vector. You also have account threat detection and response. Because, and I don't know about you, but we're seeing this every single day. People are trying to break into our Google Workspace accounts, our Microsoft 365 accounts. Material gives you comprehensive control over access and authentication of people and third-party apps.
[01:22:05] You need that information too. Material empowers organizations to rapidly mature their ability to detect and stop breaches with step-up authentication when you have extra sensitive content. Blast radius visualization for accounts, so you know what the risks are. And the ability to detect and respond to threats and risk across the entire cloud workspace. Material enables organizations to scale their security without scaling their teams.
[01:22:33] Material drives operational efficiency with its simple API-based implementation and flexible, automated, and one-click remediations for email, file, and account issues, including an AI agent that automates user report triaging and response. So it takes some of the load off of your team too. Material protects the entire workspace for the cost of just email security alone, with a simple and transparent pricing model. This is a great solution.
[01:23:01] It secures your inbox and your entire cloud workspace without adding more toil to your day or costs to your balance sheet. See? Material.security to learn more or book a demo. Again, that's material.security. Thank you so much for supporting security now. Time is right. Everybody's in the cloud these days. You need material security. All right. Let's get back to Steve.
[01:23:27] So while I was over at Bleeping Computer confirming that Lawrence Abrams had independently verified Microsoft's hard-to-believe JavaScript behavior, wow, I encountered the news that Microsoft has now also begun forcing upgrades of unmanaged Windows 11 PCs from 24H2 to 25H2. Yeah, I saw that. Yeah.
[01:23:56] Last Friday, Bleeping Computer reported, starting this week, Microsoft has begun force upgrading unmanaged devices running Windows 11 24H2 Home and Pro editions to Windows 11 25H2. According to the company's lifecycle policy report, Windows 11 24H2 will reach end of support in roughly six months on October 13, 2026.
[01:24:22] Also known as the Windows 11 2025 update, Windows 11 25H2 began rolling out in September to eligible Windows 10 or 11 devices as a minor update installed through enablement packages less than 200K in size. Microsoft said in a Monday rollout to the Windows release health dashboard, quote, the machine learning, the machine learning based intelligent rollout,
[01:24:50] because of course, Leo, everything has to be intelligent, intelligent AI nonsense now. Otherwise, it's no good, right? Right. Humans, those humans don't know what they're doing. Yeah, that's right. has expanded to all devices running Home and Pro editions of Windows 11 version 24H2 that are not managed by IT departments. Devices running these editions will no longer receive fixes for known issues,
[01:25:17] time zone updates, technical support, or monthly security and preview updates containing protections from the latest security threats. These devices will automatically receive the update to Windows 11 version 25H2 when they're ready. No actions required, and you can choose when to restart your device or postpone the update. Yeah, right. We've been there before until they start saying, do you want to do it now or later? They said those who don't want to wait for the automatic update
[01:25:47] can manually check whether the update is available in settings Windows update and click the link to download and install Windows 11 25H2. If you're not ready to update, you can also pause updates from settings Windows update by selecting the amount of time you'd like to pause them. However, you must install the latest updates after the time limit has passed. Microsoft also provides a support document and a step-by-step guide,
[01:26:17] rights-bleeping computer, to help users resolve problems encountered during the Windows 11 25H2 upgrade process. Since the March 2026 Patch Tuesday updates were released, that's last month, Microsoft has issued several emergency updates, including ones that address a known issue, breaking sign-ins with Microsoft accounts across multiple Microsoft apps, such as Teams and OneDrive,
[01:26:45] that also pushed out-of-band updates for hot patch-enabled Windows 11 Enterprise devices that fixed a Bluetooth device visibility issue and security vulnerabilities in the routing and remote access service management tool. So, I wanted to mention this because GRC's in-control freeware can also be used to give users control over exactly this process.
[01:27:15] It configures Windows to appear as if it's under management. Thus, it is not unmanaged and Microsoft will officially leave it alone. If you have used in-control to lock down your current Windows version and may wish to make the move to Windows 11 25H2, control can just be as easily reversed. So, I just saw that. I wanted to give everybody a reminder.
[01:27:44] You know, as we know, we had fun with it at the time. We go back in the Windows 7 days where the first version of this was called Never 10. Never 10. Yeah. When I vowed to never be using Windows 10. So, Never 10. And then there was a temptation to do Never 11. Never 11. But because they promised us that 10 would be the last version, I thought, nope, fool me once.
[01:28:12] You know, it's Lucy pulling the football out from under Charlie Brown. So, I decided instead to create In-Control, which would allow us, you know, once we... Apparently, there's going to be a Windows 12, right? So, okay. I'm glad I called it In-Control and not Never 11. Never 11. Never 12. You could do it. You know what, though? If you're really thinking, you could get upgrade fees every year. Just think about it. I'm just saying.
[01:28:42] Actually, it's free. So... Oh, shoot. No. You see? Yeah. You see? You see? Did want to mention that it's freeware and it was with no bugs known at the time of its release. So, it's still at release one and it works perfectly and it's free and you can use it forever. So, last week's deep dive into the Lite LLM mess revealed that the proximate cause of Lite LLM's troubles was actually the use
[01:29:11] of a compromised free and open source vulnerability scanner called Trivi. It was widely expected that Lite LLM would not be alone in this and, indeed, we've since learned that none other than Cisco Systems became another victim. Bleeping Computer also reported on this. They explained, Cisco has suffered a cyber attack after...
[01:29:39] So, Cisco has suffered a cyber attack after threat actors used stolen credentials from the recent Trivi supply chain attack to breach its internal development environment and steal source code, steal Cisco's source code belonging to the company and its customers. A source, who asked to remain anonymous, told Bleeping Computer that Cisco's Unified Intelligence Center, the CSIRT,
[01:30:09] and EOC teams contained the breach involving a malicious, and here it is, GitHub Action plugin from the recent Trivi compromise. We'll be talking about Action in a minute. They wrote, the attackers used the malicious GitHub Action to steal credentials and data from the company's build and development environment impacting dozens of devices, including some developer and lab workstations. While the initial breach has been contained,
[01:30:39] Bleeping Computer was told that the company expects continued fallout from the follow-on Light LLM and checkmarks supply chain attacks. As part of the breach, multiple AWS keys were reportedly stolen and later used to perform unauthorized activities across a small number of Cisco AWS accounts. Cisco has isolated affected systems, begun re-imaging them, and is performing a wide-scale credential rotation.
[01:31:09] I wanted to mention that one of the things that we're seeing now is that the bad guys know how to take advantage of the things they steal. Back in the early days, we were seeing AWS credentials were stolen, but then we didn't immediately hear that and they were used to ill effect for those from whom they were stolen.
[01:31:39] Now we're always seeing that. My point is that is another thing that seems to have changed is all the bad guys know how to take advantage of what it is they steal, and they know that their window of opportunity will be very short. So they immediately jump on it and, you know, their attacks go broad and deep and wide so that they're getting the most bang they can for the buck
[01:32:07] to the detriment of, you know, the victims of these. They wrote, Bleeping Computer has learned that more than 300 Cisco GitHub repositories. 300 GitHub Cisco repositories were also cloned during the incident, including source code for its AI-powered products. Of course, Cisco's going to have that. Why fix the old ones? Such as AI assistance,
[01:32:38] AI defense, and unreleased products. Whoops. Yeah. A portion of the stolen repositories allegedly belong to corporate customers, including banks, BPOs, and U.S. government agencies. Multiple sources told Bleeping Computer that more than one threat actor was involved in the Cisco CICD and AWS account breaches with varying degrees of activity. Bleeping Computer contacted Cisco with questions.
[01:33:07] I bet they did regarding the breach, but has not received a reply to our emails, they wrote. Cisco's breach was caused by this month's Trivi Vulnerability Scanner Supply Chain Attack in which threat actors compromised the project's GitHub pipeline to distribute credential-stealing malware through official releases and GitHub actions. That attack enabled the theft of CICD credentials from organizations
[01:33:37] using the tool, giving actors access to thousands of internal build environments. Security researchers linked these supply chain attacks to the Team PCP threat group based on the use of their self-titled Team PCP cloud stealer info stealer. Team PCP has been conducting a series of supply chain attacks targeting developer code platforms such as GitHub, PyPI, NPM,
[01:34:07] and Docker. The group also compromised the Lite LLM PyPI package which impacted tens of thousands of devices and the Checkmark's KICS project to deploy the same information-stealing malware. So, one snarky but understandable comment I saw from someone commenting upon the fact that some of Cisco's source code had escaped. Somebody wrote, maybe they can fix some bugs
[01:34:37] while they're in there. Yeah. We can hope. They probably could if they wanted to. Wow, wow. So, I know from seeing the domains of our Security Now listeners who have email subscriptions, the email domains in email subscriptions that the Proton family of products are very popular among our listeners. Yeah, I see a lot of app
[01:35:06] Proton.com email in our subscriber base. So, I wanted to note that last Tuesday Proton announced Proton Meet which Proton describes as a privacy-first end-to-end encrypted audio and video conferencing solution. They, Proton, explained, writing, when meeting in person isn't an option, we turn to video calls for conversations
[01:35:35] too important for email or chat. Whether you're talking to a doctor, hosting an executive meeting, or checking in with your kids, you expect these interactions to be private and safe. But mainstream video conferencing services, such as Zoom, Google, and Microsoft can eavesdrop on your conversations. Proton Meet gives you back your privacy and peace of mind by protecting your calls with
[01:36:05] end-to-end encryption so nobody can listen in or use your conversations to sell ads, conduct surveillance, or train AI. Okay, now I'll admit I was somewhat surprised by Proton's claim of eavesdropping and it appears that their are mostly referring to the leakage of metadata. Not that that's not a problem, but that seems to be their focus. Also, their information may be a bit dated and
[01:36:34] skewed. Their claims included links to Zoom, Google, and Microsoft. But for example, the Microsoft link talked about Outlook cycle, okay, and the Zoom link was a posting written six years ago in 2020. This is not to suggest that I would not be far more inclined to trust Proton than Microsoft, Google, or Zoom. I would without question. Anyway, I have the
[01:37:03] link to last week's Proton's meet announcement in the show notes for anyone who may be interested in following up, although I'm sure if you just go to Proton.me, which is the domain of this link, it probably comes up on their announcements. And I mentioned we would be talking in the future about GitHub. Well, that future is now. The recent Lite LLM and now Cisco and now several other
[01:37:33] attacks that have all been attributable to the Trivi malware scanner also involve GitHub's actions feature. In the wake of these various messes, GitHub has announced that it now plans to accelerate the development and rollout of some of the additional GitHub actions security features it had originally planned to roll out later this year. In other words, whoops,
[01:38:02] maybe sooner rather than later. So since actions are now seeing some serious abuse, there's no time like the present to improve their security, security, and that is happening. Also, Cloudflare said that in their posting, just sort of in passing, that the use of the sort of checking back in
[01:38:31] 1.1.1.1 remains super private. And this was posted on the 8th anniversary of its launch. They said exactly eight years ago today, they posted this, I guess Sunday, we launched 1.1.1.1 public DNS resolver with the intention to build the world's fastest resolver and the most private one. We knew that trust is everything for a service that
[01:39:00] handles the phone book of the internet. That's why at launch, we made a unique commitment to publicly confirm that we are doing what we said we would do with personal data. In 2020, we hired an independent firm to check our work instead of just asking you to take our word for it. We shared our intention to update such examinations in the future. We also called on other providers to do the same. But as far as we're aware, no other
[01:39:30] major public resolver has had their DNS privacy practices independently examined. So anyway, their posting continues at some length, but they were just audited by one, and this is the point, they just had an audit by one of the top four accounting firms, and they again passed with flying colors. So they do not want to know who uses their service, nor what those users
[01:40:00] look up. DNS querying source IPs are anonymized on use and deleted within 25 hours. So they are really doing everything they can to honor their privacy commitments. And Leo, we're at an hour and a half in. Let's take a break, and then I'm going to talk about the other very cool thing that Cloudflare has just done by
[01:40:30] basically creating a WordPress replacement. Very, very cool. Yeah, I think it's very interesting. We'll talk about N-Dash in just a little bit. I think that's what Steve's aiming at. Yep. But first a word from another thing to get very excited about, our sponsor, Bitwarden. I actually saw them at RSEC and it was really great to talk to them. I love what they're up to, especially if you are an AI, developer in AI,
[01:40:59] you'll love the secrets features that they're adding. Let me talk about Bitwarden. The, our sponsor for this segment of Security Now, if you didn't know, the trusted leader in passwords, passkeys, and secrets management, as I said, with over 10 million users across 180 countries and more than 50,000 businesses, Bitwarden is consistently ranked number one in user satisfaction by G2 and software reviews. Some really nice features. We, I talked with them at
[01:41:29] RSEC about a new thing they just announced, the Agent Secure Access, which is an SDK that they're making open so everybody can adopt it, that lets you use your password manager to store and deliver secrets, you know, API keys, things, tokens, things like that, to your AI without putting them in clear text, anywhere on your hard drive, all the security of the Bitwarden vault, all the convenience of having AI be able to get it,
[01:41:59] but not reveal it and not whatever it does, not committed to GitHub. They're always adding new features, it's so great. I've been using their SSH key generator, another great idea because now I just keep all my SSH keys in Bitwarden, I don't have to maneuver them and move them around, I have it all there, Bitwarden's on every machine so it makes it very simple. With Bitwarden access intelligence, this is for enterprise, another great feature, organizations can
[01:42:29] use Bitwarden to identify weak, reused, or exposed credentials and coach your employees to take action immediately, which is great, they become part of your security team. While vault health alerts, which they've had for some time, and password coaching, surface risk to individual users in real time, and guide them to fix issues on the spot, turning one of the most common causes of breaches into something visible, prioritized, and fixable.
[01:42:59] And now, let me talk about this new agent access SDK. This is so cool. This is what we interviewed them about at RSEC. I love it that they're making it open. I mean, first for me, that was the thing that blew me away. Instead of saying, no, this is ours, it's proprietary, no one else can use it, they want everybody to use it, which makes it that much more useful. It's a powerful way for developers and teams to securely integrate controlled credential access, the kind you get from Bitwarden, into applications, automation
[01:43:29] workflows, and AI agents. It enables programmatic just-in-time access to vault-stored credentials without exposing sensitive data, supporting their secure use within modern development environments. This release does not incorporate any AI functionality, I think they want to make this clear, into the Bitwarden solution. Don't worry, they're not doing that. And, maybe even as importantly, does not grant AI systems persistent or unrestricted access to vault data. That's why
[01:43:58] it's an SDK. The agent access SDK is a separate open-source development toolkit designed to enforce secure human-approved and scoped credential access for teams that leverage AI agents in their workflows. I immediately installed it. It was exactly what I needed. It's available now in an early alpha phase for testing. The agent access SDK introduces a secure framework for how agents request, receive, and use credentials, helping define a model for
[01:44:28] safe credential interaction in agent-driven systems. Of course, they've got the Bitwarden MCP as well, another way of keeping your credentials secure while making it easier to get your job done. Bitwarden now enables passkey logins everywhere. I love passkeys. You can do it now with Windows 11. Yes, securely unlocking devices at the OS level. Now, of course, they had to work with Microsoft on this. They're working with Microsoft on native passkey support
[01:44:57] in Windows 11, and this also extends SSO to automatically log users into more apps, which makes credential management across devices more seamless than ever. It makes users extremely happy. Trust me, as a user, I know that. For people who are looking for a self-hosted lightweight option, look for Bitwarden Lite. It offers a self-hosted password manager designed for home labs, personal projects, just any kind of quick deployment, minimal overhead,
[01:45:26] and total control. If you're a trust-knowing person, you're going to love Bitwarden Lite. You've got to know that Bitwarden's open source code is regularly audited by third-party experts. You can go visit it and look at it yourself. It's on GitHub, GPL licensed. It meets SOC 2, type 2, GDPR, HIPAA, CCPA standards, ISO 27001-2002. It's completely secure, it's implemented right, and it's open, and that's so important. Get started
[01:45:56] today with Bitwarden's free trial of a Teams or enterprise plan for your business, or get started for free forever across all devices as an individual at bitwarden.com slash twit. That's bitwarden.com slash twit. I know I loaded you up with a bunch of new features, but they're loading us up with a bunch of new features. They are really amazing. They are working hard and doing a great job. bitwarden.com slash twit. It's the only password
[01:46:26] manager I use and the one I recommend. Okay, Steve, on we go. Okay, so, oh, I guess it was on April 1st. So, because I started this with also on April 1st, Cloudflare announced, so that must have been on April 1st that they were talking about their 1.1.1.1 DNS. Also on April 1st, Cloudflare announced their M-DASH, E-M-D-A-S-H. For those who don't know, there are, there's a
[01:46:55] regular hyphen style dash, then there are dashes that are the width of an N and the width of an M. And so M-DASH is what they call this. I don't really know why, but it's kind of just a cool name. Anyway, it caught my eye and I'm sure it will. Actually, many of our listeners sent the announcement to me, so I knew they were aware of it, because its goal,
[01:47:25] M-DASH, the M-DASH project's goal is to replace WordPress with a far more secure successor. And, you know, the expression far more secure in the case of WordPress is not a high bar, since, you know, every security now listener knows quite well what a complete security disaster WordPress has become. And it's
[01:47:55] creaky old architecture, which Cloudflare has just completely replaced. The source of WordPress's trouble has been that it promises to allow anyone to author and offer an insecure WordPress plugin, and that its architecture doesn't allow security containment of those. Unfortunately, many people have taken them up on this and the
[01:48:25] result is a mess. So here's what we learned from Cloudflare. They wrote, the cost of building software has, oh, AI, the cost of building software has drastically decreased. We recently rebuilt the most popular React framework, Next.js, in one week using AI coding agents. But for the past two months, our agents have been working on an even
[01:48:54] more ambitious project, rebuilding the WordPress open source project from the ground up. They wrote, WordPress powers over 40% of the internet. It is a massive success that has enabled anyone to be a publisher and created a global community of WordPress developers. But the WordPress open source project will be 24 years old this year. Hosting a website has changed
[01:49:24] dramatically during that time. When WordPress was born, AWS EC2 didn't exist. In the intervening years, that task has gone from renting virtual private servers to uploading a JavaScript bundle to a globally distributed network at virtually no cost. It's time to upgrade the most popular content management system, CMS, on the internet to take advantage of this change.
[01:49:54] Our name for this new CMS is M-Dash. We think of it as the spiritual successor to WordPress. It's written entirely in TypeScript. It is serverless, but you can run it on your own hardware or any platform you choose. Plugins are securely and can run in their own isolate via dynamic workers, solving the fundamental security problem with the WordPress plugin
[01:50:24] architecture. Under the hood, M-Dash is powered by Astro, the fastest web framework for content driven websites. M-Dash is fully open source, MIT licensed, and available on GitHub. While M-Dash aims to be compatible with WordPress functionality, no WordPress code was used to create M-Dash. That allows us to license the open source project under the more permissive MIT
[01:50:53] license, as opposed to GPL. We hope that allows more developers to adapt, extend, and participate in M-Dash's development. You can deploy the M-Dash version 0.1.0 preview to your own Cloud Flare account or to any Node.js server today as part of our early development beta. Okay, so all of that is super
[01:51:23] interesting. But what about WordPress's security, right? Before we get to that, Cloud Flare felt the need to congratulate WordPress and kind of apologize, I think, a little bit for replacing it. So they wrote, the story of WordPress is a triumph of open source that enabled publishing at a scale never before seen. Few projects have had the same recognizable impact on the generation raised on the internet. The contributors to WordPress's
[01:51:53] core and its many thousands of plugin and theme developers have built a platform that democratized publishing for millions, many lives and livelihoods being transformed by this ubiquitous software. There will always be a place for WordPress, but there's also a lot more space for the world of content publishing to grow. A decade ago, people picking up a keyboard universally learned to publish their blogs with WordPress. Today, it's just as
[01:52:22] likely that person picks up Astro or another TypeScript framework to learn and build with. The ecosystem needs an WordPress years ago. Emdash is committed to building upon what WordPress created, an open source publishing stack that anyone can install and use at little cost, while fixing the core problems that WordPress
[01:52:52] cannot solve. And here it comes. WordPress's plugin architecture, they wrote, is fundamentally insecure. 96% of security issues for WordPress sites originate in plugins. In 2025, more high severity vulnerabilities were found in the WordPress ecosystem than in the previous two years combined.
[01:53:22] In other words, things with WordPress are getting worse, not better. They wrote, why after over two decades, is WordPress plugin security so problematic? A WordPress plugin is a PHP script that hooks directly into WordPress to add or modify functionality. There is no isolation. A WordPress plugin has direct
[01:53:52] access to the WordPress site's database and file system. When you install a WordPress plugin, you are trusting it with access to nearly everything and trusting it to handle every malicious input or edge case perfectly. MDash solves this. In MDash, each plugin runs in its own isolated sandbox, a dynamic worker. Rather than
[01:54:21] giving direct access to underlying data, MDash provides the plugin with capabilities via bindings based on what the plugin explicitly declares it needs in its manifest. This security model has a strict guarantee an MDash plugin can only perform the actions explicitly declared in its manifest. You can know and trust up front before
[01:54:51] installing a plugin exactly what you are granting it permission to do similar to going through an OAuth flow and granting a third party app a specific set of scoped permissions. WordPress plugin security is such a real risk that WordPress.org manually reviews and approves each plugin in its marketplace. At the time of writing that review
[01:55:21] queue is over 800 plugins long and takes at least two weeks to traverse. The vulnerability surface area of WordPress plugins is so large that in practice all parties rely on marketplace reputation ratings and reviews. And because WordPress plugins run in the same execution context as WordPress itself and are so deeply intertwined with
[01:55:51] WordPress code, some argue they must carry forward WordPress's GPL license. These realities combine to create a chilling effect on developers building plugins and on platforms hosting WordPress sites. Plugin security is the root of this problem. Marketplace businesses provide trust when parties otherwise cannot easily trust each other. In the case of the
[01:56:21] WordPress marketplace the plugin security risk is so large and probable that many of your customers can only reasonably trust your plugin via the marketplace but in order to be part of the marketplace your code must be licensed in a way that forces you to give it away for free everywhere other than that marketplace in other words you are locked in so that's the gist of it their posting continues at much greater
[01:56:50] length but everyone gets the idea right Cloudflare has leveraged AI agency to take the conceptual promise that WordPress met and to dramatically overhaul its architecture for licensing freedom and security essentially it is a plug-in architecture where these dynamic workers are running as their own
[01:57:19] execution spaces they communicate to this new m-dash core via an API and controlled by the manifest which they explicitly define and export right up front so it is the architecture you would design today if you wanted to do what WordPress has
[01:57:49] been doing but to do it in a secure fashion and on GitHub all open all open source MIT license means you can do much more with it if you wish so another big home run I think for for Cloudflare yeah it's very interesting I you know I hope they support it and I mean clearly they want to take over the 40% of the internet that's run by WordPress
[01:58:19] and they probably have pretty credible reason to yeah I think if we see a core of add-ons emerge which solve the problems that people have and you look at the security model that it offers why if you were starting from scratch would you use a WordPress CMS as opposed to an MDash CMS there's another reason for them doing this they want to make
[01:58:49] something that is easily manipulated by AI that an AI could build a website easily build a website on and while AI can certainly do that with WordPress I think this is designed specifically with that I bet you are what happened so
[01:59:19] that it's well as I said at the top of the show by the time we're done here everyone will have a very clear sense and understanding for what it means and how it may change we'll see why it makes no sense I mean it really really really doesn't good well I'm really really interested in your take but that's
[01:59:49] coming up after this word from our sponsor hox hunt and you're going to want to know about this one we have you're to
[02:00:18] to learn how to respond to phishing attempts but you try to train them and then what do you get the eye rolls right during the training and you can't really blame them the one size fits all you know phishing simulations your employees spot them from a mile away the report button that gets ignored more often than not your programs are running but it's not changing employee behavior meanwhile
[02:00:48] AI is making real attacks more convincing by the day and leadership is starting to ask the question you don't have a clear answer to is this actually working well Hoxhunt was and it does it just like social media does it through
[02:01:18] personalized gamified micro training powered by AI and behavioral science training your employees will enjoy will love and when people like what they're learning as opposed to fighting it they learn and you'll love it as an admin because Hoxhunt does all the heavy lifting in fact I was just talking to Russell who's been setting this across email but not just email
[02:01:47] slack teams because you know bad guys get in any way they can the emails are personalized to each employee based on role location and behavior just like the phishing every simulation uses AI to mirror real world attacks meaning employees are being tested on what's actually getting through not some outdated template they go please give me a break they recognize it immediately and because it's gamified it keeps engagement high
[02:02:17] without feeling punitive and because every interaction generates a coaching moment you're not just tracking completion you're actively building behavioral indicators that tell a real story reporting rates repeat clicker reduction and time to report the kind of metrics that hold up when leadership asks those hard questions but you don't have to take our word for it with over 3,500 verified reviews on G2 Hawks Hunt is the top rated security training platform recognized
[02:02:47] for best results and easiest to use is also recognized as customer's choice by Gartner and used by thousands of companies Qualcomm DocuSign Nokia they all trust it to train millions of employees worldwide visit hawkshunt.com security now today to learn why modern secure companies are making the switch to Hawks Hunt that's hawkshunt.com security now h-o-x-h-u-n-t dot com slash
[02:03:16] security now I can't wait I know we're going to get some of these simulations soon I don't want to be the one guy who falls for them I really don't but you know what that's nice one of the nice things is to give you gold stars they don't punish you they don't make you look dumb they reward you for the right behavior and that's the way to do it all right speaking of behavior this is exactly the right behavior the FCC has banned all routers made outside the US
[02:03:47] which is to say all routers see all yes anyone encountering the news which landed two weeks ago
[02:04:24] on March surprise edition of every consumer router to the so-called covered list means that the likes of ASUS Linksys Netgear Eero TP-Link D-Link and Nest have all suddenly joined the likes of previously banned non-consumer devices made by Huawei ZTE Hytera and HickVision the headline that appeared in the
[02:04:54] afternoon 15 days ago read FCC updates covered list to include this is the FCC's own press release they so their headline is FCC updates covered list to include foreign made consumer routers the press release explained that the full title was FCC updates covered list to include foreign made consumer routers
[02:05:23] prohibiting approval of new models so all of the existing apparently attack prone and buggy routers can still be sold but anything that's new and hopefully improved is banned yay for the US's national security the official fact sheet that accompanied the press release included the helpful subhead
[02:05:53] update follow up this update follows determination by executive branch agencies that consumer grade routers produced in foreign countries threaten national security okay so I need I need to share some more of what the FCC wrote because it's not even internally consistent the press releases fact sheet says Washington
[02:06:23] March 23rd 2026 today the federal communications commission updated its covered list to include all consumer grade routers produced in foreign countries routers are the boxes in every home that connect computers phones and smart devices to the internet this followed a determination by a white house convened executive branch interagency body with appropriate national
[02:06:53] security expertise that such routers quote pose unacceptable risks to the national security of the United States or the safety and security of United States persons unquote it continues the executive branch determination noted that foreign produced routers one introduce a supply chain vulnerability that could disrupt the U.S. economy critical
[02:07:22] infrastructure and national defense and two pose a severe cyber security risk that could be leveraged to immediately and severely disrupt U.S. critical harm U.S. persons unquote President Trump's 2025 national security strategy stated quote the United States must never be dependent on any
[02:07:52] outside power for core components from raw materials to parts to finished products necessary to the nation's defense or economy we must re-secure our own independent and reliable access to the goods we need to defend ourselves and preserve our way of life unquote malicious actors they wrote have exploited security gaps in foreign made routers which again
[02:08:22] routers to attack American households disrupt networks enable espionage and facilitate intellectual property theft foreign made routers again all routers were also involved in the vault flax and salt typhoon cyber attacks targeting vital US infrastructure as well it wasn't my link sis
[02:08:51] okay sorry as outlined below today's action does not impact a consumer's here it is a consumer's continued use of routers they previously acquired nor does it prevent retailers from continuing to sell import or market router models approved previously through the FCC's equipment authorization process
[02:09:21] by operation of the FCC's covered list rules the restrictions imposed today apply to new device models okay wait it just said today's action does not impact a consumer's continued use of routers they previously acquired nor does it prevent retailers from continuing to sell import or
[02:09:51] market router models approved previously through the FCC's equipment authorization process so in other words every single one of the existing apparently suddenly untrustworthy routers that everyone in the world already has are going to be left alone where they are after all what else can be done consumers already own those this means that
[02:10:21] foreign manufacturers which again is to say all router manufacturers are prevented from introducing any new router models into the US they're free to keep making the existing routers and they're also presumably free to keep updating those routers firmware which might be used to add new features or eliminate bugs we would hope but that would mean that as
[02:10:50] Wi-Fi technologies continue advancing and requiring support from new chipsets and new radio hardware newer routers cannot be obtained from traditional foreign suppliers okay that happened Monday afternoon 15 days ago by the end of that week the technology policy institute a Washington based non-profit think tank
[02:11:20] published an analysis of this action which I think is extremely useful and worth understanding because it compares what just happened to the previously enacted and outwardly similar ban on Huawei and ZTE equipment for the policy that for the technology policy institute Scott Walston titled his piece the FCC got the router
[02:11:50] ban wrong it banned all new foreign made routers from the U.S. commercial market by adding them to its so-called covered list the action followed a White House convened interagency national security determination issued just three days earlier the commission took this action with no
[02:12:20] notice and comment proceeding no published cost benefit analysis and without providing a broad transition process for the affected industry the only path forward for manufacturers is to apply for conditional approval from the Department of Defense or the Department of Homeland Security I'll note that the actual documentation about this which I
[02:12:49] read which requires this conditional approval to be obtained is from the U.S. of War or the DHS Scott appears to be choosing to use the department's earlier name so he continues the security concerns he writes are real Chinese state sponsored hacking groups including Volt Typhoon Salt Typhoon and
[02:13:19] Flax Typhoon have exploited vulnerabilities in consumer routers to penetrate American networks conduct surveillance and build bot nets for attacks on critical infrastructure okay now I'm I'm not taking issue with what Scott wrote here but I do want to take the time to note that to the best of my knowledge none of our current consumer grade routers ship in an
[02:13:49] inherently vulnerable state it's true that in years past meaning more than a decade ago more than 10 years ago we were encountering instances and we discussed them on the podcast where for example Intel's demonstration only source code for their UPnP implementation was unfortunately dropped directly into routers this
[02:14:18] resulted in UPnP being bound to consumer routers WAN facing network interfaces essentially by mistake after delivering a podcast about that the next week I announced that I had enhanced shields ups services to explicitly allow visitors to check for public UPnP exposure but all of that was fixed back in 2013 and 2014 12 years ago at the time
[02:14:48] many people were exposed that we fixed that we as an industry fixed it also back then as in more than 10 years ago we encountered instances where ISP provided routers had open ISP admin ports they were either using weak authentication credentials or known authentication credentials or contained remotely exploitable weaknesses but for
[02:15:18] quite some time now it has only been when a router's user deliberately configures their router to allow external connections and thus to implicitly solicit external attacks that any of the various Chinese typhoons Volt Salt or Flax might have been able to get into users networks through those routers my point is for quite some time now like for the past 10
[02:15:47] years it's been users who have been unwittingly causing these external open port exposure problems and none of that would be lessened by routers having domestic points of origin thus nothing the FCC is attempting to do will fix anything that is now broken Scott continues writing router security
[02:16:17] deserves serious attention but in the past the FCC addressed threats like these in a way that was more targeted more precisely designed and better built to survive a legal challenge comparing the FCC's handling of the Huawei and ZTE threat in the 2019 through 2022 to the new router ban reveals what happens when an agency abandons
[02:16:47] the deliberative process that makes its expertise useful to respond to the national security risks posed by Huawei and ZTE the FCC followed a deliberative process and produced a carefully constructed regulatory framework Congress identified the specific companies as threats in Section 889 of the fiscal year 2019
[02:17:17] National Defense Authorization Act the FCC designated Huawei and ZTE as national security threats in June of 2020 published its initial covered list in March of 2021 and adopted a notice of proposed rulemaking and notice of inquiry on June 17, 2021 initiating two separate dockets and inviting public comment the commission then adopted
[02:17:46] a report and order in November of 2022 with a unanimous four to zero vote and simultaneously issued a further notice of proposed rulemaking seeking additional comment on issues it hadn't yet resolved that process took time but it also produced outcomes that it could never have achieved in a weekend now we could argue that's bureaucracy and bureaucracy
[02:18:15] has overhead and it takes time but what it does is it tends to keep it from making mistakes and as he said just deciding to do it over the weekend and then doing it well you get the kind of things that we've been seeing from this administration for the last year and three months the comment process he writes produced differentiated
[02:18:45] treatment based on actual risk the FCC did not treat all five Chinese companies identically it fully banned new Huawei and ZTE equipment but took a more nuanced approach with HIC vision Daowa and Hytera the FCC agreed with commenters who argued that these companies pose different levels and kinds of risks the FCC
[02:19:15] required those three companies to document the safeguards they would put in place and froze their applications pending that review the router ban by contrast that is this one treats a net gear router assembled in Vietnam identically to a TPLINK router designed in China the comment process identified a clear scope the FCC had to define what counted
[02:19:44] as covered equipment for example it established that handset equipment designed for broadband operation with connection speeds of at least 200 kilobits per second fell within the scope of telecommunications equipment while equipment below that threshold did not that line was not in the original proposal it emerged from the comment process as affected companies argued that basic radio equipment should not
[02:20:14] be now draws no such lines its definition of produced in a foreign country encompasses any major stage in the process through which the device is made including manufacturing assembly
[02:20:44] design and development potentially sweeping in routers designed by American companies and assembled overseas as they all are the Huawei ZTE response included transition assistance the FCC's decision imposed real costs on carriers rural carriers told the FCC they couldn't afford to remove Huawei and ZTE equipment without financial help Congress responded
[02:21:13] by creating the secure and trusted communications networks reimbursement program initially funded at a 1.9 billion level which funded the removal and replacement of insecure equipment from carrier networks the program has problems such as a lack of evaluation and careful tracking of funds okay maybe some waste fraud and abuse but if the cost imposed on a company is due to a government mandate the government should
[02:21:43] at least consider how to pay for it fortunately that doesn't apply here nothing really changes for consumers he wrote the comment process produced legal durability during the rulemaking commenters raised constitutional challenges including arguments that the rules were an unconstitutional bill of attainder violated the equal protection clause and amounted to an unconstitutional taking of property the
[02:22:13] FCC addressed each of these arguments in its order building a legal record when Huawei challenged the related NDAA restrictions in court a federal district court found the restrictions lawful because the government had demonstrated they reasonably furthered non-punitive national security goals the router ban meaning what's happened now has no comparable record
[02:22:42] and former FCC officials have already predicted it will face legal challenge also he writes the FCC recognized that its initial rules were a first step and continued refining them a second report and order clarified that covered equipment includes modular transmitters proposed a definition of critical infrastructure and sought further comment on the
[02:23:12] scope of marketing prohibitions the agency learned from industry input how supply chains actually work and adjusted its rules accordingly none of this happened with the router ban the White House convened a panel the panel issued a determination routers bad three days later the FCC implemented it although the secure networks act leaves the FCC little
[02:23:42] discretion over whether to add items to the covered list once the White House makes a qualifying determination the FCC still retains substantial leeway over how to implement the resulting equipment authorization restrictions including its scope transition periods and what guidance it issues for affected parties meaning it still could have done more he writes in the Huawei ZTE proceeding the covered list edition itself was relatively quick
[02:24:12] but the FCC spent more than a year designing the implementing rules through a public process nothing in the secure networks act prevented the FCC from doing the same here it chose not to the router ban bears all the hallmarks of and to those who have been watching
[02:24:41] watching Washington recently what a shock the stated the stated jurisdiction is cyber security risk from foreign manufacturing but the evidence the FCC itself cited undercuts the case for a foreign country of manufacture approach according to the department of justice volt typhoon primarily targeted cisco
[02:25:11] and netgear routers devices designed by american companies the routers were vulnerable not because of where they were manufactured but because those companies had stopped providing security updates for the discontinued models and i'll just note that's true in the case of netgear volt typhoon leveraged routers whose firmware had never been updated and was thus very old
[02:25:41] and also exposed management interfaces with weak credentials so again it's nothing about country of origin scott continues the fbi's own guidance urged router owners to replace end of life devices and cissa's mitigation advice to manufacturers focused on secure design and automated updates not supply chain origin
[02:26:10] salt typhoon compromised major u.s. telecommunications carriers through network equipment made by cisco though cisco's own security researchers reported that most intrusions it reviewed involved stolen credentials rather than software vulnerabilities the national security determination includes supporting evidence from nist cissa and the fbi and other agencies on router vulnerabilities
[02:26:40] generally but none of it pervade persuasively establishes that country of production standing alone is a useful proxy for cyber security risk and agents basically the white house just you know waved the wand you know waved a hand and said let's outlaw foreign made routers period all those bad consumer routers were you know were outlawing them an agency he writes
[02:27:10] exercising careful judgment would have noticed this disconnect if the problem is that manufacturers abandon security updates for older devices the solution might be to mandate some kind of software maintenance or to require vulnerability disclosures not a blanket import ban organized around the country of manufacture the FCC has an interdisciplinary expert staff who could have evaluated
[02:27:40] whether country of origin is actually a useful proxy for cyber security risk given the speedy timeline it seems unlikely that meaning three days it seems unlikely that they were consulted in any meaningful way in principle country of manufacture could matter in hardware supply chains if a state actor could theoretically compromise hardware during production this
[02:28:09] concern is real and deserves a serious policy response but a blanket ban covering routers from every country on earth is not that response a targeted action against manufacturers with documented ties to adversarial intelligence services combined with supply chain integrity requirements for all manufacturers seeking FCC authorization would address the hardware concern far
[02:28:39] more precisely that's roughly what the FCC did with Huawei and ZTE but the current ban treats a router from Finland the same as one from China making the matter worse is that virtually no consumer grade routers are manufactured in the United States that only widely cited exception is some Starlink Wi-Fi routers that
[02:29:09] SpaceX says are made in Texas even major American brands including Netgear Eero and Google manufacture their requires companies to disclose their management structure detail their supply chain and present a plan for on-shoring manufacturing
[02:29:39] to the United States that's what this really is this is about manufacture not security right what a shock yes yes and he writes that is not a security audit it is industrial policy masquerading as a national security framework no comment period helped shape it and while there are extensive submission requirements there appears to be no public review timeline
[02:30:09] or clear decision standard meanwhile the ban creates the very vulnerability it claims to address firmware and software updates for existing covered devices are permitted through at least thanks to a blanket waiver from the FCC's office of engineering and technology but that waiver expires a router that cannot
[02:30:38] receive security updates becomes exactly the kind of unpatched vulnerable device that Volt Typhoon and Salt Typhoon exploited some may argue that the post Salt Typhoon threat environment necessitates faster action than the multi-year Huawei process allowed but if that is true it becomes hard to justify an action that does nothing about the millions
[02:31:07] of foreign made routers already deployed in American homes and businesses which are the actual devices that Volt Typhoon and Salt Typhoon exploited if the threat were urgent enough to justify bypassing all deliberation one would expect the FCC to be taking emergency action on the installed base it is not the ban
[02:31:37] addresses only future models making this a forward looking regulatory action for which a deliberative process was both feasible and appropriate a serious response would combine targeted restrictions on specific manufacturers with supply chain integrity and software maintenance requirements for all manufacturers seeking FCC authorization the FCC has the expertise
[02:32:06] to design such a framework and it did exactly that with Huawei and ZTE in December testimony before the Senate Commerce Committee Chairman Carr told lawmakers that the FCC is not an independent agency formally speaking the router ban is a case study in what happens when that posture translates into skipping
[02:32:36] the processes that make regulation work the comparison between the Huawei ZTE process and the router ban is not just a story about two different policy decisions it is a controlled experiment in what deliberative process is worth same agency same statutory framework same category of threat but the 2019 through 2022 process in which the FCC
[02:33:06] used its full deliberative toolkit produced targeted bans differentiated treatment based based based risk precise scoping informed informed by industry expertise billions in transition funding and a legal record durable enough to survive court challenge the 2026 process in which the commission used none of those tools produced a blanket ban on an entire product category
[02:33:36] without differentiation no scoping analysis no transition assistance and a legal record so thin that former FCC officials are already predicting litigation the secure networks act is the mechanism that enables this arrangement under the statute the FCC says it cannot update the covered list on its own but rather must implement determinations made by national
[02:34:05] security agencies when those determinations were narrow and entity specific this was a manageable arrangement and the FCC still exercised its own judgment in designing the implementation rules now that the determinations have expanded to cover entire product categories and the FCC has chosen not to exercise its implementation authority the agency is implementing sweeping trade and technology policy
[02:34:35] without the deliberation such decisions require the same rapid implementation pattern produced the December 2025 ban on foreign made drones which is already being challenged in court in that case section 1709 of the fiscal year 2025 national defense authorization act gave national security agencies one year to complete an evidence based review of DJI
[02:35:05] drones with an automatic covered list addition as a fallback instead of a targeted review of DJI the executive branch again issued a broad national security determination covering all foreign made drones which the FCC implemented immediately DJI has since sued to challenge the action and he finishes process is
[02:35:34] not bureaucratic waste of time it is the mechanism through which an agency's expertise improves the quality of its decisions the FCC demonstrated this in 2022 when it banned Huawei and ZTE equipment through a deliberative process that produced a more targeted more durable and more precisely designed result whatever the reasons the commission did not follow the same approach here meaning
[02:36:04] the FCC the outcome speaks for itself Congress should pay attention the secure networks act created a mechanism that when combined with sweeping executive branch determinations and an FCC willing to implement them without deliberation allows the president to ban entire categories of consumer technology without notice
[02:36:34] without comment without cost benefit analysis and without any of the procedural safeguards that normally govern consequential regulatory action if Congress intended the covered list to be used this way it should say so if it didn't it should act before the next product category lands on the list okay so where does this leave us
[02:37:02] this apparently arbitrary and short sided ban will do exactly nothing to actually improve the security of any existing routers whose current models may continue to be sold since new routers cannot be sold one effect may be to freeze current model numbers where they are unfortunately major generational router
[02:37:32] improvements have multi year design development and manufacturing pipelines this means that all of the router manufacturers will currently have their future planned models in the process of becoming ready for market next year later this year next year except that now that market has just been killed for them that suggests that Scott is probably correct about future lawsuits
[02:38:02] under the terms of this ban even domestic manufacturers incorporated in the United States whose equipment is made offshore which is to say all routers will need to appeal to the conditional approval process which as Scott noted requires companies to disclose their management structure detail their supply chain and present a plan for on shoring manufacturing to the United States what
[02:38:31] a mess with any luck saner heads will prevail or competent management of the FCC will be installed it doesn't appear that we currently have that I'll finish off today's look at actual consumer security with a little sanity check reminder nearly everyone now has IoT network technology running inside
[02:39:00] their network security perimeter that establishes and maintains through their NAT router persistent connections and many if not most of these phone home and maintain persistent connections are to servers located outside the US as I've been noting for many years now these devices which we blithely invite into our homes to set up their own shops
[02:39:30] could do far more damage to actual damage to consumer security than any routers designed within the last decade we have invited them inside our network they can see our networks management interface at 192.168.0.1 or .1.1 or wherever it is and no one's monitoring them for all we know they are busy right now trying to brute force that management interface
[02:40:00] but you know don't tell anyone in Washington or they might become the FCC's next misguided target it's just I mean it's so frustrating I wanted to share this because it really puts in context how arbitrary this was how it doesn't achieve anything whereas the previous ban on Huawei and ZTE actually did it
[02:40:29] identified a problem substantiated the problem and surgically excised what needed to be removed and then helped to pay for the removal and replacement of this Chinese gear that with good reason we decided we could not trust having inside the US infrastructure any longer instead this just says we're banning any new foreign made routers crazy I mean
[02:40:59] it's absolutely does nothing yeah and one hopes that it is so errant errant that it'll somehow get fixed it's just hard to believe it will continue meanwhile I don't know what we're going to do I guess built you know you got instructions don't you on your website to build like a PF sense router right yes it is just not a problem any longer to
[02:41:29] get a little fanless PC and use actually open sense OPN sense is now the one to switch to PF senses you know open sense grew out of it and is I think probably the better choice and you put it on what is that little box that you put it on I can't remember the name of that it's it's a
[02:41:59] cute little thing yeah it's a cute little thing somebody in the chat room will say because I know they yeah there is a little it's called the SG 1100 although it has nothing to do with Steve Gibson but well that's it that's all you need is the SG 1100 and you run open sense I'm sure you can run it's from Netgate yes net gate that's right yeah yeah and that's a cute little guy now they
[02:42:33] there's another little platform I bought one on Amazon it's the one I'm using over in my place with Lori it's got four network interfaces I can't remember the name of it now but on it I'm also using PF sense just because I know PF sense but if somebody need to solve
[02:43:03] the radio connection problem separately but PF sense is a very powerful little routing software it has all the security features you could want really we're up to Wi-Fi 7 now and so what this is saying is we cannot ever get a Wi-Fi 8 router because that would require a new model number to make it yeah
[02:43:35] it's just nuts 40% of all the routers in the United States are made by TP-Link a Chinese company that's the one they were going to ban initially then they said well what you
[02:44:05] comment on this FCC decision it happened that morning and they did not want to talk about it there's no it was and I understand why it's no win what are they going to say we don't like the idea no we like the idea no no comment no comments the only thing you can say the only safe thing to say unless they have plans to build a factory in Piscataway I don't know what else they're going to do I think that's the
[02:44:35] plan right well everybody has to build routers in a router factory they are just lining up and all the consumers will be happy to pay an extra hundred bucks for domestic manufacturing to get nothing in return I mean it's like well the routers are no more secure just because they're made in the US doesn't mean anything no they're less
[02:45:05] frankly yeah and I'm sure this net gate is not made in the US no nothing is made in the US nothing nothing we don't make things here oh well that's the mistake I mean admittedly it probably should create well the mistake is being is like rattling sabers between us and we ought to just have a detente
[02:45:35] here and say look you know you want us to buy your stuff we want you to make the stuff that that that that we're gonna buy so come on let's wrap this up because in about half an hour we're about to bomb Iran into the stone age so I got pushed back by two weeks oh what a shock I know a taco that's right we got it we got a two week what a shocker that happened during the podcast during one of I I got a little what a stunning stunning
[02:46:05] development who would have thought okay well I'm actually I'm I'm relieved to be asked I'm as I'm sure 90 million Iranians are thank you sir you are you are a gentleman and a scholar and I appreciate everything you do Mr. Steve Gibson you'll find him at grc.com that is the place to go
[02:46:35] to get of course the things he makes for a living which include spin right the world's best mass storage maintenance recovery and performance enhancing utility current version 6.1 awesome awesome tool everybody who has mass storage needs it let's just say that also the DNS benchmark pro which just came out that's available at the same place 10 999 save it save a penny 999
[02:47:05] although there are no pennies anymore either so they've gone the way of the American of the foreign main router what else while you're there you might want to check out you can send Steve email if you want but you got to get your email address whitelisted because he doesn't want spam by going to grc.com slash email and when you give them your email you'll notice there's two boxes below it that you can check they're unchecked by default but you can say hey I would like to get your weekly mailing
[02:47:34] of the show notes for the show or hey I would like to know when you've got a new product you might get something in the next hundred years you might not it's not exactly an active mailing list but it is it is a mailing list and you can get on it grc.com slash email there's lots of other great stuff it's well worth browsing around a great site meanwhile we have of course copies of the show at our website twit.tv slash sn there's a youtube channel you can go to with all
[02:48:04] the shows video of them great way to share a clip and of course you can subscribe in your favorite podcast client and get it automatically the minute we're done fixing it up you can if you want it faster than that you can watch live we do the show every tuesday right after mac break weekly that would be 1 30 pacific 4 30 eastern 20 30 utc we stream it live on youtube twitch x.com facebook linkedin and kick also
[02:48:34] club members get access to it behind the velvet rope if it as it were in the club twit discord so you know sign up for the club that's a great way to get ad-free versions of the show special access our ai user group it's coming up club twit steve thank you so much
[02:49:03] great to see you we'll see you again next week yes sir for the but will that be there 14th we'll be back taco tuesday thank you steve take care bye hi i'm leo laporte host of this week in tech and many other shows on the twit podcast network can you believe it 2026 is around the corner so this my friends is the best time to grow your brand with twit nobody understands the tech audience better than
[02:49:33] we do we love our audience and we know how to effectively message to them we develop genuine relationships with brands creating authentic promotions that resonate with our highly engaged community of tech enthusiasts you know over 90% of twit's audiences involved in their company's tech and it decision making night can you believe that 90% 88% have actually made a purchase based on a twit post red ad
[02:50:03] no one comes close we're the best at this as one twit fan said I've bought from twit tv sponsors because I trust Leo and his team's knowledge of the latest tech if twit and twit trust you cannot buy trust like that well actually you can you can buy that on twit all our ads are unique they're read live by our expert host Micah Sargent me we simulcast all during the shows on our social platforms so everybody can be watching live
[02:50:33] you know one of our customers Harun Mir the founder of Thinks Canary he's been with us since 2016 since 2016 he said we expected twit to work well for us because we were long time listeners who over the years bought many of the products and services we learned about on various twit shows and we were not disappointed the combination of the very personal ad reads and the careful selection of products that twit largely believes in gives the ads an authentic trusted voice that works really well
[02:51:02] for our products 10 out of 10 we'll use again thank you Harun we love you and it's been nine years that's kind of that's the proof over delivery of impressions you get presence on show episode pages so there's a link right there that our audience can click on we're in the rss feed descriptions a link there too and social media promotion our full service team will craft compelling creative
[02:51:32] to elevate your brand and support you throughout your entire campaign I work on the copy myself to make it authentic to make it real if you want to reach a passionate tech audience through a network that consistently over delivers please contact us directly partner at twit.tv that's the email address partner at twit.tv let's talk about how we can help grow your brand or just go to twit.tv slash advertise for more information I look
[02:52:02] forward to working the on the back hitziger debattieren as in the police say about what tablet la is what the cable schneller läd and why 100 times the trick film a grundrecht is our auto are absolutely wach because
[02:52:32] regardless of roadtrip or a trip if your flight has your akku right off or you have hunger to have what you have then we for you here enterprise here for you